Assault surfaces are rising quicker than safety groups can sustain. To remain forward, it is advisable know what’s uncovered and the place attackers are almost certainly to strike. With cloud migration dramatically rising the variety of inner and exterior targets, prioritizing threats and managing your assault floor from an attacker’s perspective has by no means been extra necessary. Let’s take a look at why it is rising, and monitor and handle it correctly with instruments like Intruder.
What’s your assault floor?
First, it is necessary to know that your assault floor is the sum of your digital belongings which might be ‘uncovered’ – whether or not the digital belongings are safe or weak, recognized or unknown, in energetic use or not. This assault floor modifications constantly over time, and contains digital belongings which might be on-premises, within the cloud, in subsidiary networks, and in third-party environments. In brief, it is something {that a} hacker can assault.
What’s assault floor administration?
Assault floor administration is the method of discovering these belongings and companies after which decreasing or minimizing their publicity to forestall hackers exploiting them. Publicity can imply two issues: present vulnerabilities resembling lacking patches or misconfigurations that scale back the safety of the companies or belongings. However it may additionally imply publicity to future vulnerabilities.
Take the instance of an admin interface like cPanel or a firewall administration web page – these could also be safe in opposition to all recognized present assaults right this moment, however a vulnerability might be found within the software program tomorrow – when it instantly turns into a major danger. An asset does not have to be weak right this moment to be weak tomorrow. When you scale back your assault floor, no matter vulnerabilities, you turn into more durable to assault tomorrow.
So, a major a part of assault floor administration is decreasing publicity to doable future vulnerabilities by eradicating pointless companies and belongings from the web. This what led to the Deloitte breach and what distinguishes it from conventional vulnerability administration. However to do that, first it is advisable know what’s there.
Asset administration vs vulnerability administration
Usually thought of the poor relation of vulnerability administration, asset administration has historically been a labour intensive, time-consuming activity for IT groups. Even after they had management of the {hardware} belongings inside their group and community perimeter, it was nonetheless fraught with issues. If only one asset was missed from the asset stock, it may evade your entire vulnerability administration course of and, relying on the sensitivity of the asset, may have far reaching implications for the enterprise.
At the moment, it is a complete lot extra sophisticated. Companies are migrating to SaaS and transferring their programs and companies to the cloud, inner groups are downloading their very own workflow, mission administration and collaboration instruments, and particular person customers count on to customise their environments. When corporations broaden by mergers and acquisitions too, they usually take over programs they are not even conscious of – a basic instance is when telco TalkTalk was breached in 2015 and as much as 4 million unencrypted data have been stolen from a system they did not even know existed.
Shifting safety from IT to DevOps
At the moment’s cloud platforms allow improvement groups to maneuver and scale rapidly when wanted. However this places quite a lot of the duty for safety into the fingers of the event groups – shifting away from conventional, centralized IT groups with sturdy, trusted change management processes.
This implies cyber safety groups battle to see what’s going on or uncover the place their belongings are. Equally, it is more and more arduous for big enterprises or companies with dispersed groups – usually situated around the globe – to maintain monitor of the place all their programs are.
Consequently, organizations more and more perceive that their vulnerability administration processes must be baked right into a extra holistic ‘assault floor administration’ course of since you should first know what you will have uncovered to the web earlier than you consider what vulnerabilities you will have, and what fixes to prioritize.
Important options of assault floor administration instruments
Varied instruments in the marketplace are good for asset discovery, discovering new domains which seem like yours and recognizing web sites with related content material to your personal. Your staff can then verify if it is a firm asset or not, select whether or not it is included in your vulnerability administration processes, and the way it’s secured. However this requires an inner useful resource as a result of the instrument cannot do that for you.
Equally, some instruments focus solely on the exterior assault floor. However since a standard assault vector is thru worker workstations, assault floor administration ought to embody inner programs too. Listed here are three important options that each assault floor monitoring instrument ought to present:
1. Asset discovery
You’ll be able to’t handle an asset if you do not know it exists. As we have seen, most organizations have quite a lot of “unknown unknowns,” resembling belongings housed on companion or third-party websites, workloads working in public cloud environments, IoT gadgets, deserted IP addresses and credentials, and extra. Intruder’s CloudBot runs hourly checks for brand spanking new IP addresses or hostnames in linked AWS, Google Cloud or Azure accounts.
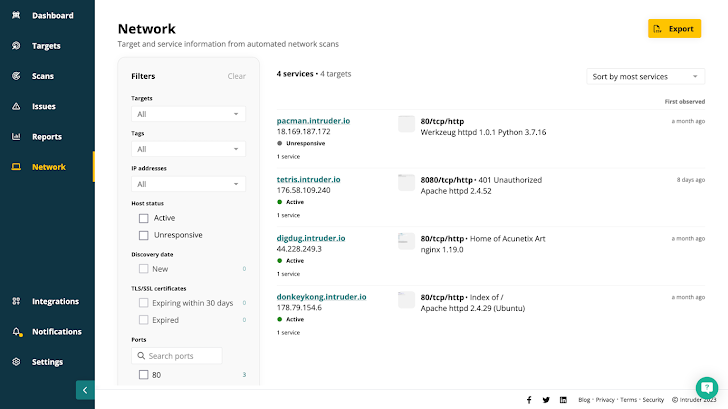
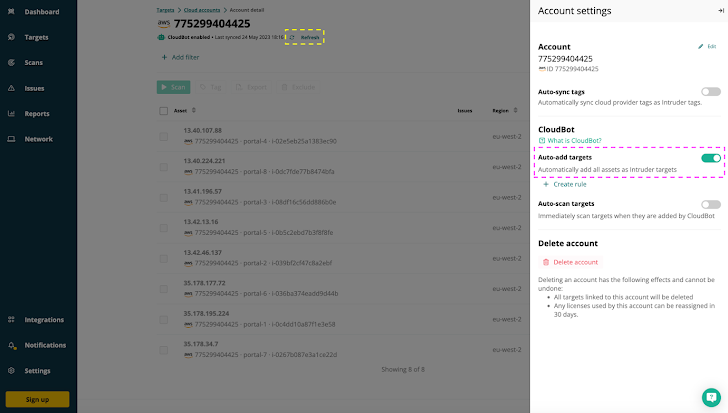 |
| Intruder’s CloudBot mechanically provides any new exterior IP addresses or hostnames in cloud accounts as targets for monitoring & vulnerability scanning. |
2. Enterprise context
Not all assault vectors are created equal and the ‘context’ – what’s uncovered to the web – is a crucial a part of assault floor administration. Legacy instruments do not present this context; they deal with all assault surfaces (exterior, inner workplace, inner datacentre) the identical, and so it is arduous to prioritize vulnerabilities. Assault floor administration instruments establish the gaps in your inner and exterior safety controls to disclose the weaknesses in your safety that have to be addressed and remediated first.
Intruder takes this a step additional and supplies perception into any given asset, and the enterprise unit the applying belongs to. For example, realizing whether or not a compromised workload is part of important utility managing bank-to-bank SWIFT transactions will aid you formulate your remediation plan.
3. Proactive and reactive scans
You’ll be able to’t simply check your assault floor as soon as. Day by day it continues to develop as you add new gadgets, workloads, and companies. Because it grows the safety danger grows too. Not simply the danger of latest vulnerabilities, but additionally misconfigurations, information exposures or different safety gaps. It is necessary to check for all doable assault vectors, and it is necessary to do it constantly to forestall your understanding from turning into outdated.
Even higher than steady scanning is a platform that may scan proactively or reactively relying on the circumstances. For instance, reacting to a brand new cloud service being introduced on-line by launching a scan, or proactively scanning all belongings as quickly as new vulnerability checks turn into accessible.
Decreasing your assault floor with Intruder
Assault floor monitoring instruments like Intruder do all this and extra. Intruder makes certain that every thing you will have going through the web is meant to be – by making it simply searchable and explorable. Its Community View function reveals precisely what ports and companies can be found, together with screenshots of people who have web sites or apps working on them.
Most automated instruments are nice at spitting out information for analysts to have a look at, however not at decreasing the ‘noise’. Intruder prioritizes points and vulnerabilities primarily based on context, or whether or not they need to be on the web in any respect. Mixed with Intruder’s steady monitoring and rising menace scans, this makes it a lot simpler and faster to seek out and repair new vulnerabilities earlier than they are often exploited.
Attempt Intruder for your self!
With its assault floor monitoring capabilities, Intruder is fixing some of the elementary issues in cybersecurity: the necessity to perceive how attackers see your group, the place they’re prone to break in, and how one can establish, prioritize and remove danger.Able to get began ?