Researchers this month uncovered a two-year-old Linux-based distant entry trojan dubbed AVrecon that enslaves Web routers into botnet that bilks on-line advertisers and performs password-spraying assaults. Now new findings reveal that AVrecon is the malware engine behind a 12-year-old service known as SocksEscort, which rents hacked residential and small enterprise units to cybercriminals seeking to cover their true location on-line.
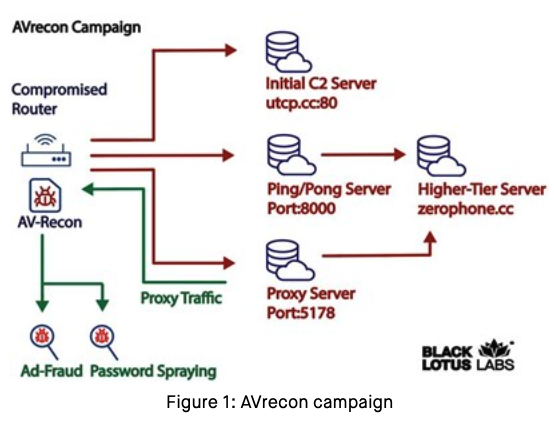
Picture: Lumen’s Black Lotus Labs.
In a report launched July 12, researchers at Lumen’s Black Lotus Labs known as the AVrecon botnet “one of many largest botnets concentrating on small-office/home-office (SOHO) routers seen in current historical past,” and a criminal offense machine that has largely evaded public consideration since first being noticed in mid-2021.
“The malware has been used to create residential proxy companies to shroud malicious exercise corresponding to password spraying, web-traffic proxying and advert fraud,” the Lumen researchers wrote.
Malware-based anonymity networks are a serious supply of undesirable and malicious net visitors directed at on-line retailers, Web service suppliers (ISPs), social networks, e-mail suppliers and monetary establishments. And an important many of those “proxy” networks are marketed primarily to cybercriminals searching for to anonymize their visitors by routing it by way of an contaminated PC, router or cellular gadget.
Proxy companies can be utilized in a professional method for a number of enterprise functions — corresponding to value comparisons or gross sales intelligence — however they’re massively abused for hiding cybercrime exercise as a result of they make it troublesome to hint malicious visitors to its authentic supply. Proxy companies additionally let customers seem like getting on-line from almost anyplace on the earth, which is helpful if you happen to’re a cybercriminal who’s making an attempt to impersonate somebody from a selected place.
Spur.us, a startup that tracks proxy companies, advised KrebsOnSecurity that the Web addresses Lumen tagged because the AVrecon botnet’s “Command and Management” (C2) servers all tie again to a long-running proxy service known as SocksEscort.
SocksEscort[.]com, is what’s often known as a “SOCKS Proxy” service. The SOCKS (or SOCKS5) protocol permits Web customers to channel their Net visitors by way of a proxy server, which then passes the knowledge on to the meant vacation spot. From a web site’s perspective, the visitors of the proxy community buyer seems to originate from a rented/malware-infected PC tied to a residential ISP buyer, not from the proxy service buyer.
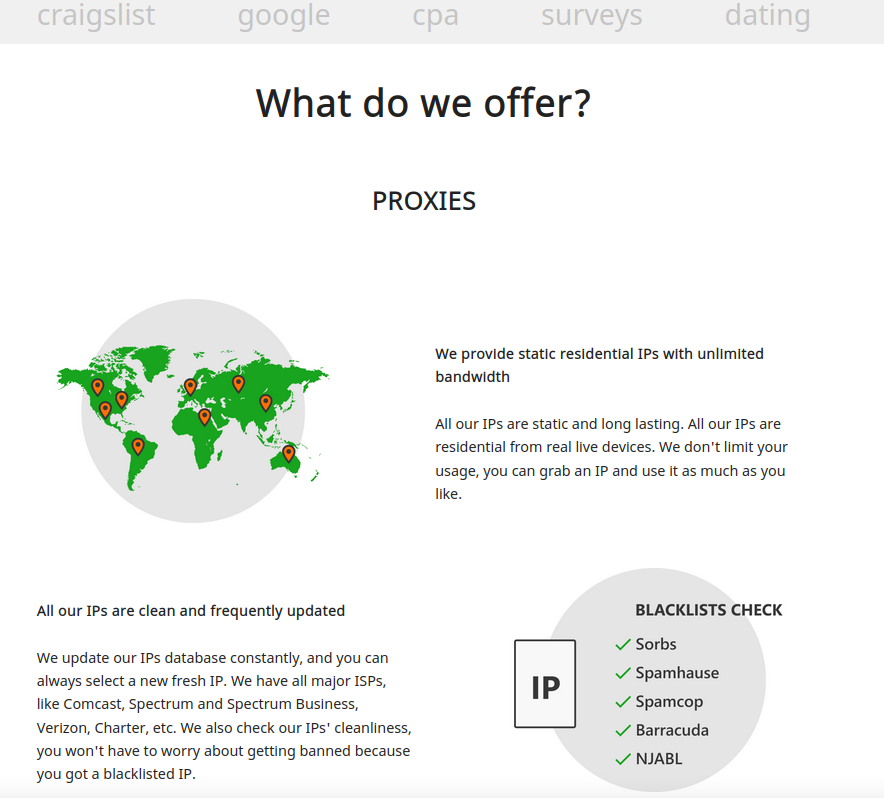
The SocksEscort house web page says its companies are good for individuals concerned in automated on-line exercise that always ends in IP addresses getting blocked or banned, corresponding to Craigslist and courting scams, search engine outcomes manipulation, and on-line surveys.
Spur tracks SocksEscort as a malware-based proxy providing, which suggests the machines doing the proxying of visitors for SocksEscort clients have been contaminated with malicious software program that turns them right into a visitors relay. Often, these customers do not know their techniques are compromised.
Spur says the SocksEscort proxy service requires clients to put in a Home windows primarily based software to be able to entry a pool of greater than 10,000 hacked units worldwide.
“We created a fingerprint to establish the call-back infrastructure for SocksEscort proxies,” Spur co-founder Riley Kilmer mentioned. “Taking a look at community telemetry, we had been in a position to verify that we noticed victims speaking again to it on numerous ports.”
In keeping with Kilmer, AVrecon is the malware that provides SocksEscort its proxies.
“When Lumen launched their report and IOCs [indicators of compromise], we queried our system for which proxy service call-back infrastructure overlapped with their IOCs,” Kilmer continued. “The second stage C2s they recognized had been the identical because the IPs we labeled for SocksEscort.”
Lumen’s analysis staff mentioned the aim of AVrecon seems to be stealing bandwidth – with out impacting end-users – to be able to create a residential proxy service to assist launder malicious exercise and keep away from attracting the identical stage of consideration from Tor-hidden companies or commercially obtainable VPN companies.
“This class of cybercrime exercise menace could evade detection as a result of it’s much less doubtless than a crypto-miner to be seen by the proprietor, and it’s unlikely to warrant the amount of abuse complaints that internet-wide brute-forcing and DDoS-based botnets usually draw,” Lumen’s Black Lotus researchers wrote.
Preserving bandwidth for each clients and victims was a major concern for SocksEscort in July 2022, when 911S5 — on the time the world’s largest identified malware proxy community — obtained hacked and imploded simply days after being uncovered in a narrative right here. Kilmer mentioned after 911’s demise, SocksEscort closed its registration for a number of months to stop an inflow of latest customers from swamping the service.
Danny Adamitis, principal data safety researcher at Lumen and co-author of the report on AVrecon, confirmed Kilmer’s findings, saying the C2 information matched up with what Spur was seeing for SocksEscort courting again to September 2022.
Adamitis mentioned that on July 13 — the day after Lumen revealed analysis on AVrecon and began blocking any visitors to the malware’s management servers — the individuals accountable for sustaining the botnet reacted shortly to transition contaminated techniques over to a brand new command and management infrastructure.
“They had been clearly reacting and making an attempt to keep up management over parts of the botnet,” Adamitis mentioned. “Most likely, they wished to maintain that income stream going.”
Frustratingly, Lumen was not in a position to decide how the SOHO units had been being contaminated with AVrecon. Some attainable avenues of an infection embrace exploiting weak or default administrative credentials on routers, and outdated, insecure firmware that has identified, exploitable safety vulnerabilities.
WHO’S BEHIND SOCKSESCORT?
KrebsOnSecurity briefly visited SocksEscort final 12 months and promised a follow-up on the historical past and attainable id of its proprietors. A assessment of the earliest posts about this service on Russian cybercrime boards suggests the 12-year-old malware proxy community is tied to a Moldovan firm that additionally gives VPN software program on the Apple Retailer and elsewhere.
SocksEscort started in 2009 as “super-socks[.]com,” a Russian-language service that bought entry to 1000’s of compromised PCs that might be used to proxy visitors. Somebody who picked the nicknames “SSC” and “super-socks” and e-mail deal with “michvatt@gmail.com” registered on a number of cybercrime boards and commenced selling the proxy service.
In keeping with DomainTools.com, the apparently associated e-mail deal with “michdomain@gmail.com” was used to register SocksEscort[.]com, super-socks[.]com, and some different proxy-related domains, together with ip-score[.]com, segate[.]org seproxysoft[.]com, and vipssc[.]us. Cached variations of each super-socks[.]com and vipssc[.]us present these websites bought the identical proxy service, and each displayed the letters “SSC” prominently on the high of their homepages.
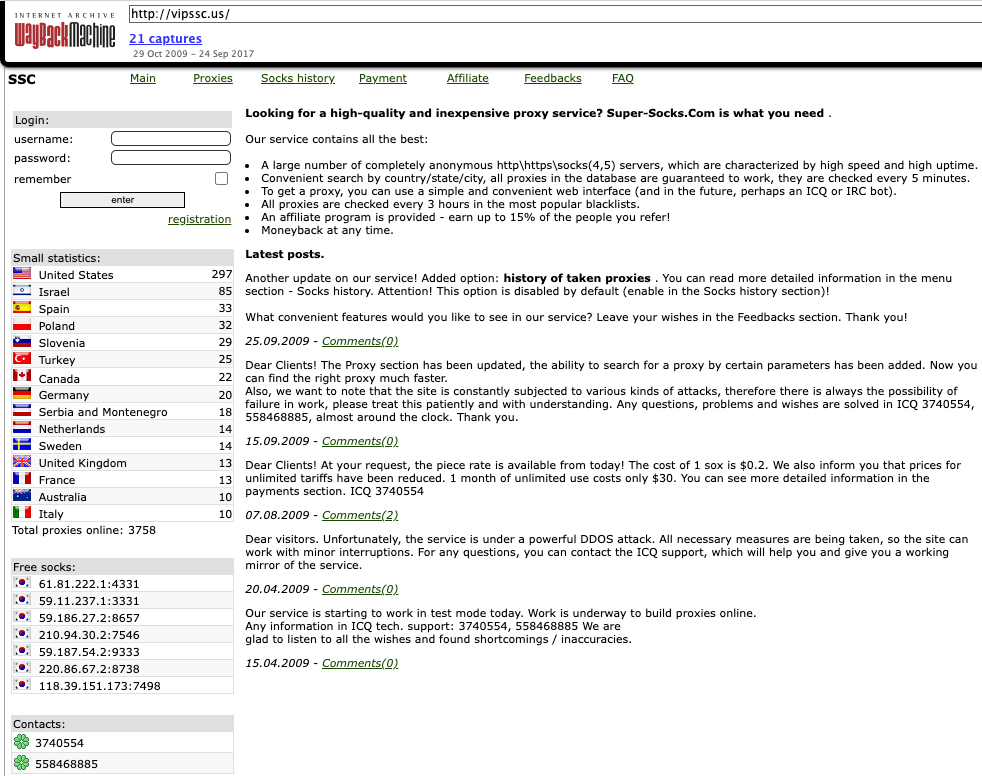
Picture: Archive.org. Web page translation from Russian through Google Translate.
In keeping with cyber intelligence agency Intel 471, the very first “SSC” id registered on the cybercrime boards occurred in 2009 on the Russian language hacker group Antichat, the place SSC registered utilizing the e-mail deal with adriman@gmail.com. SSC requested fellow discussion board members for assist in testing the safety of a web site they claimed was theirs: myiptest[.]com, which promised to inform guests whether or not their proxy deal with was included on any safety or anti-spam block lists.
DomainTools says myiptest[.]com was registered in 2008 to an Adrian Crismaru from Chisinau, Moldova. Myiptest[.]com is now not responding, however a cached copy of it from Archive.org reveals that for about 4 years it included in its HTML supply a Google Analytics code of US-2665744, which was additionally current on greater than a dozen different web sites.
Many of the websites that after bore that Google monitoring code are now not on-line, however almost all of them centered round companies that had been just like myiptest[.]com, corresponding to abuseipdb[.]com, bestiptest[.]com, checkdnslbl[.]com, dnsbltools[.]com and dnsblmonitor[.]com.
Every of those companies had been designed to assist guests shortly decide whether or not the Web deal with they had been visiting the positioning from was listed by any safety corporations as spammy, malicious or phishous. In different phrases, these companies had been designed in order that proxy service customers may simply inform if their rented Web deal with was nonetheless protected to make use of for on-line fraud.
One other area with the Google Analytics code US-2665744 was sscompany[.]web. An archived copy of the positioning says SSC stands for “Server Help Firm,” which marketed outsourced options for technical assist and server administration. The corporate was situated in Chisinau, Moldova and owned by Adrian Crismaru.
Leaked copies of the hacked Antichat discussion board point out the SSC id tied to adriman@gmail.com registered on the discussion board utilizing the IP deal with 71.229.207.214. That very same IP was used to register the nickname “Deem3n®,” a prolific poster on Antichat between 2005 and 2009 who served as a moderator on the discussion board.
There was a Deem3n® consumer on the webmaster discussion board Searchengines.guru whose signature of their posts says they run a preferred group catering to programmers in Moldova known as sysadmin[.]md, and that they had been a techniques administrator for sscompany[.]web.
That very same Google Analytics code can be now current on the homepages of wiremo[.]co and a VPN supplier known as HideIPVPN[.]com.
Wiremo sells software program and companies to assist web site house owners higher handle their buyer critiques. Wiremo’s Contact Us web page lists a “Server Administration LLC” in Wilmington, DE because the dad or mum firm. Data from the Delaware Secretary of State point out Crismaru is CEO of this firm.
Server Administration LLC is at the moment listed in Apple’s App Retailer because the proprietor of a “free” VPN app known as HideIPVPN. The contact data on Crismaru’s LinkedIn web page says his firm web sites embrace myiptest[.]com, sscompany[.]web, and hideipvpn[.]com.
“The easiest way to safe the transmissions of your cellular gadget is VPN,” reads HideIPVPN’s description on the Apple Retailer. “Now, we give you an excellent simpler means to hook up with our VPN servers. We are going to cover your IP deal with, encrypt all of your visitors, safe all of your delicate data (passwords, mail bank card particulars, and so on.) type [sic] hackers on public networks.”
Mr. Crismaru didn’t reply to a number of requests for remark. When requested in regards to the firm’s obvious connection to SocksEscort, Wiremo responded, “We don’t management this area and nobody from our staff is linked to this area.” Wiremo didn’t reply when offered with the findings on this report.
