Again in 2010, a nuclear plant in Natanz, Iran, fell sufferer to the Stuxnet malware that focused Simatic Step 7, a software program product for configuring and working programmable logic controllers (PLCs). The assault allowed hackers to take advantage of the PLC models throughout the manufacturing unit and injury virtually one thousand uranium enrichment centrifuges, delivering a extreme blow to the nation’s nuclear program.
Within the case of Iran, this was not essentially a nasty factor; we do not really need extra nuclear weapons round, can we?
However think about it was your manufacturing unit, your gear price a number of million {dollars} apiece, and your fame at stake.
It is all the time helpful to place issues into perspective, proper?
What we’re driving at right here: your small business can not afford to take cybersecurity calmly. Notably, in the event you function in extremely aggressive sectors like manufacturing and provide chain administration. And particularly if your organization has tapped into the Web of Issues software program growth – similar to 72% of your rivals.
From detecting anomalies in gear efficiency earlier than failures happen to monitoring stock ranges in actual time utilizing RFID tags and BLE beacons, there are lots of thrilling IIoT purposes and advantages to think about. And simply as some ways your IIoT resolution may compromise your whole IT infrastructure, resulting in the next penalties:
- Broken equipment
- Manufacturing downtim
- Accidents on the manufacturing unit flooring
- Knowledge breach
- Reputational injury
- And direct and oblique monetary losses brought on by all the above
What are the important thing elements placing IIoT safety in danger – and the way may your organization foresee and clear up the Industrial Web of Issues safety challenges earlier than catastrophe strikes?
Let’s clear up the riddle collectively!
Rundown of IIoT safety faults and challenges
For readability’s sake, let’s outline the Industrial Web of Issues and its expertise parts earlier than zooming in on IIoT safety implications.
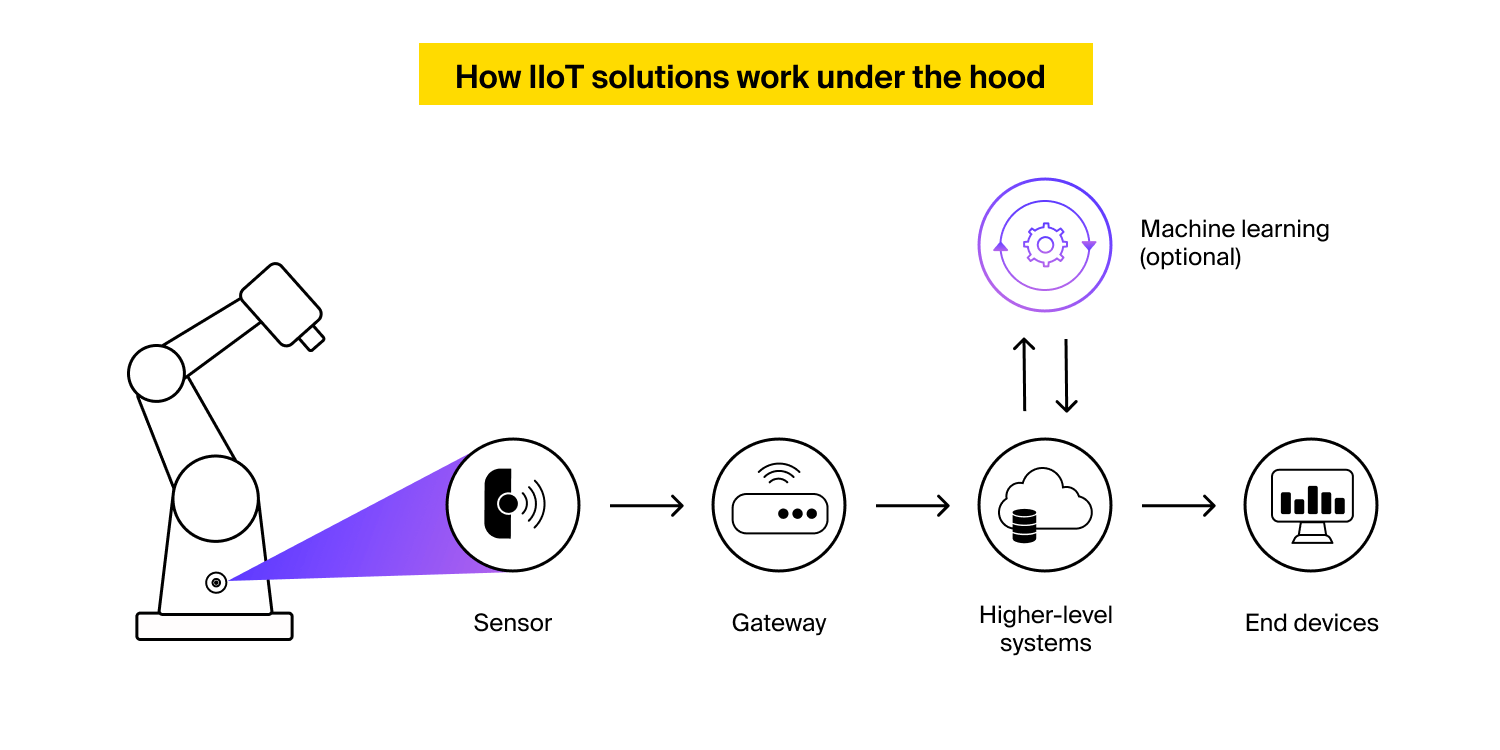
The IIoT time period refers back to the interconnected community of machines, sensors, controllers, and techniques that talk and alternate information with one another and central platforms in industrial settings.
Such cyber-physical techniques mix components of conventional industrial gear with connectivity, information analytics, and information visualization. Firms flip to IIoT consultants to observe manufacturing and warehouse operations and automate single processes or whole workflows.
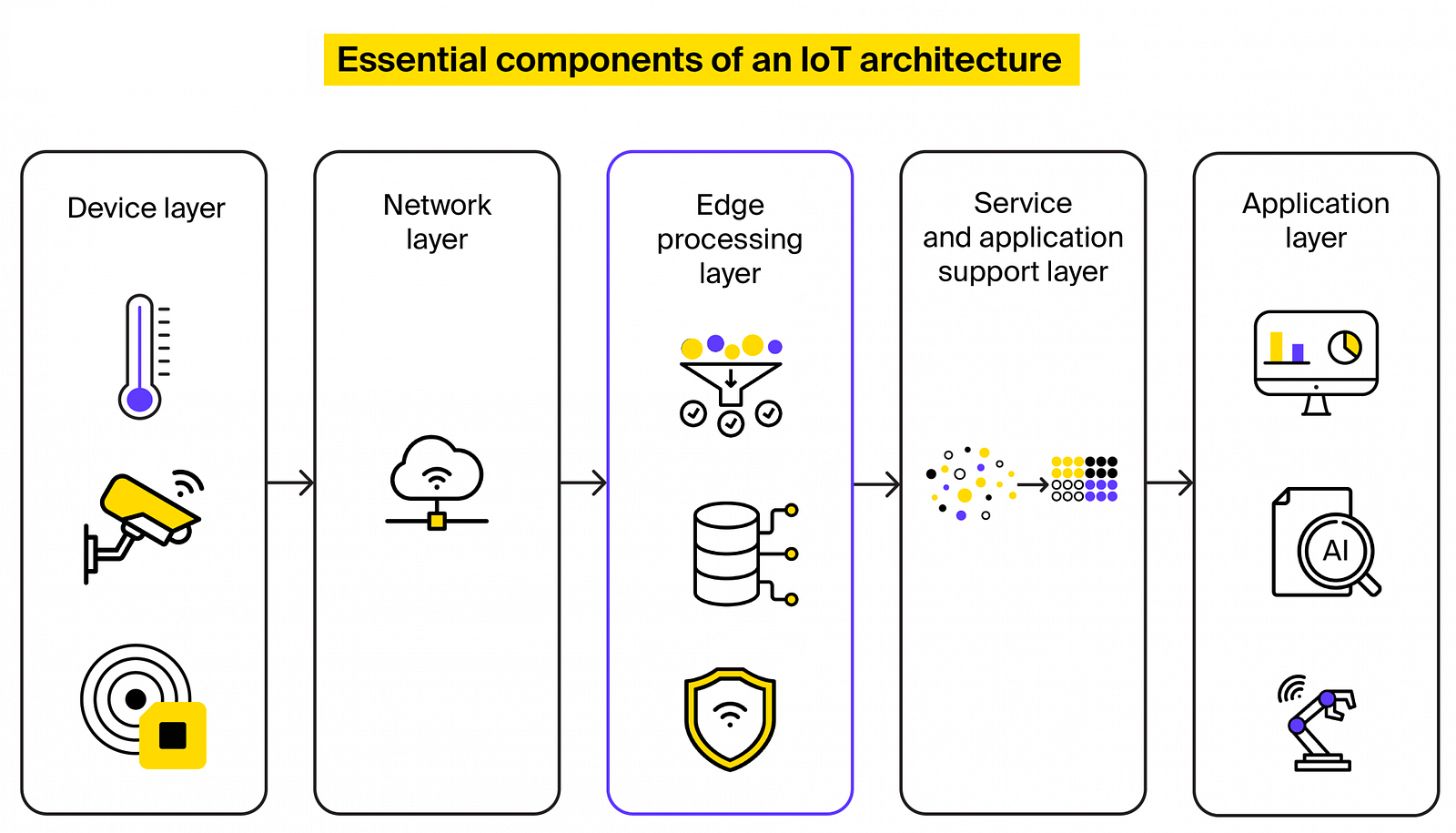
Behind the scenes, the Industrial IoT has the identical structure as each different Web of Issues resolution, though edge IoT deployments the place information is analyzed nearer to sensors prevail in industrial settings.
Firms tapping into IIoT might procure brand-new gear enhanced with sensors and supporting connectivity by default or improve current equipment utilizing customized and off-the-shelf IIoT retrofit kits.
From the Industrial IoT safety standpoint, why is it essential to know how IIoT techniques perform behind the scenes?
IIoT safety points can manifest themselves at each tier of your cyber-physical system – from programmable controllers to legacy apps containing unpatched vulnerabilities. To mitigate IIoT safety dangers, your organization ought to thus shield all endpoints in your wired or wi-fi community, safe information in transit and at relaxation, and patch safety loopholes in purposes comprising your IT infrastructure.
With out additional ado, let’s examine what elements undermine safety in IIoT options – and what you are able to do to protect your cyber-physical techniques from these threats.
Problem #1: Unsecured communications
Connectivity applied sciences are the spine of all IoT techniques, irrespective of the complexity and space of software.
In industrial settings, as extra units and sensors log on, extra endpoints, communication channels, and information storage options emerge. And this requires a really numerous and, ideally, balanced combination of information and networking protocols assembly particular IIoT safety necessities.
At present, as much as 98% of all IoT site visitors is unencrypted, that means hackers can simply bypass the primary line of protection – e.g., by studying a person’s login and password by way of a phishing assault – and lay their fingers in your firm’s information.
Poor encryption practices stem from utilizing legacy communication applied sciences, equivalent to Modbus, Profibus, and DeviceNet. In truth, many of the legacy IIoT communication protocols lack information encryption capabilities altogether, forcing IoT builders to search for workarounds, equivalent to implementing VPNs and safe tunnels or gateways and addressing encryption points on the Safe Sockets Layer (SSL)/Transport Layer Safety (TLS) degree.
Resolution
To safe information alternate between the parts of an IIoT resolution and thus forestall the Industrial Web of Issues safety accidents, we advocate you implement a fail-proof connectivity tech stack consisting of:
- Dependable information protocols. In Industrial IoT, information protocols decide how data is structured, encoded, and interpreted by units. If your organization opts for a wired IIoT deployment, you could possibly facilitate information alternate between linked gear and gateways by the Ethernet protocols, equivalent to Profinet, EtherNet/IP, and Modbus TCP/IP. Whereas these protocols don’t inherently assist information encryption, your IIoT builders can nonetheless make information unreadable to 3rd events by implementing the TLS/SSL tech stack on the transport layer or introducing middleman units, equivalent to safe gateways or firewalls, between linked units and the community. Must you search for a extra versatile information protocol for IIoT and industrial automation options, we extremely advocate the OPC Unified Structure (OPC UA) protocol, which helps end-to-end encryption, employs X.509 digital certificates for machine authentication, and can be utilized in each wired and wi-fi IIoT options. When constructing wi-fi IIoT techniques, the ITRex staff often sticks to Message Queuing Telemetry Transport (MQTT), Constrained Utility Protocol (CoAP), Superior Message Queuing Protocol (AMQP), WebSockets, or RESTful APIs with HTTPS. These fashionable protocols provide encryption capabilities by TLS/SSL or Datagram Transport Layer Safety (DTLS) and assist set up safe communication channels between linked gear, gateways, and cloud servers. For extra details about information protocols and their impression on Industrial IoT safety, ebook a free session with our R&D staff.
- Safe networking protocols. Not like information protocols, which largely take care of data alternate and interoperability, community protocols outline guidelines, requirements, and procedures for a way units are linked, how information is transmitted, and the way the parts of an IIoT system work together inside a community. From the Industrial IoT safety standpoint, networking protocols could be engaging targets for hackers. Some causes for that embody restricted entry management and authentication mechanisms and an absence of information encryption capabilities. Relying in your community structure – i.e., point-to-point, star, or mesh patterns – and meant use circumstances, you’ll be able to make the most of numerous networking protocols to deal with IIoT safety challenges. These protocols span Knowledge Distribution Service (DDS), Low Energy Broad Space Community (LoRaWAN), Zigbee, WirelessHART, and Narrowband IoT (NB-IoT). To pick the suitable connectivity tech stack assembly all your IIoT safety wants, it is very important think about the kind of cyber-physical system you are trying to construct, the required information transmission vary, and energy consumption necessities. This may be achieved throughout the discovery part of your IoT venture.
Problem #2: Insufficient software program replace practices
Not like computer systems, tablets, and smartphones, IoT units don’t assist endpoint safety techniques, equivalent to antivirus packages – just because they usually run extremely custom-made or outdated embedded software program or are particularly designed to be small and energy-efficient.
Whilst you can partially clear up Industrial IoT safety challenges by introducing firewalls, intrusion detection and prevention (IDP), and machine management mechanisms on the community degree, upgrading the purposes constituting your IIoT software program ecosystem to the most recent model turns into vital for resolving doable IIoT safety points.
Talking of IIoT software program, we have to draw the road between embedded techniques, equivalent to firmware, middleware, and working techniques (OSs), and extraordinary software program – assume internet, desktop, and cellular purposes facilitating machine administration.
Because of IIoT machine design constraints and a lot of endpoints inside a cyber-physical system, patching IIoT software program safety vulnerabilities is a process few industrial corporations can handle. That is why as much as 65% of producers nonetheless use outdated working techniques ridden with zero-day safety vulnerabilities.
Resolution
To mitigate IIoT cybersecurity dangers, an industrial firm will need to have an environment friendly software program replace administration mechanism in place.
Right here at ITRex, we’re robust advocates of software program and firmware updates over the air (OTA). On this situation, a cloud-based platform powered by AWS IoT System Administration, Azure IoT Hub, or pre-configured SaaS options like Bosch IoT Rollouts mechanically delivers software program updates to edge units, controllers, and gateways.
A correctly configured machine administration platform may also maintain higher monitor of your machine fleet, optimize replace rollouts contemplating device-specific settings and safety necessities, and notify your IT staff in emergencies.
Problem #3: Poor bodily safety measures
Community IIoT safety apart, a cyber-aware industrial firm also needs to forestall cybercriminals and malicious insiders from stealing {hardware} with the objective of scanning the units’ inside and infesting them with viruses and spying packages.
Inadequate bodily safety measures not solely compromise the integrity and confidentiality of delicate information, but in addition result in service disruptions, operational downtime, and monetary losses. The repercussions of bodily safety vulnerabilities can lengthen past the instant impression, doubtlessly endangering public security and important infrastructure.
Resolution
To deal with the poor bodily safety points in industrial IoT, a multi-faceted method is required. Here is what your organization ought to do as a part of the bodily IIoT safety overhaul:
- Prioritize the implementation of sturdy entry management mechanisms. This consists of measures equivalent to role-based entry management (RBAC) to linked gear, biometric authentication, pc imaginative and prescient-powered video surveillance, and the implementation of intrusion detection techniques
- Conduct common bodily safety audits and danger assessments. The Industrial Web of Issues safety audits assist determine vulnerabilities early on and develop acceptable mitigation methods. This proactive method permits organizations to remain one step forward of potential threats and take preventive measures to safeguard their IIoT techniques. In apply, this implies disconnecting units with proof of tampering from the community, hiding producer markings on the units, and, when doable, eradicating pointless IIoT resolution parts to stop reverse engineering occasions
- Implement complete worker coaching packages. Elevating consciousness about bodily safety dangers and greatest practices is essential to fortifying the Industrial Web of Issues cybersecurity (extra on that later). Collaboration between IT and bodily safety groups can be important. This partnership ensures a holistic method to safety, the place each digital and bodily elements are thought-about and synchronized to offer strong safety in opposition to rising IIoT safety threats.
Problem #4: Restricted visibility into machine and community exercise
As much as 90% of organizations report having shadow IoT units on their community, with 44% of the respondents admitting these units had been linked with out the data of their safety or IT groups.
Because of this, corporations are unaware of which units talk with one another, what data they collect and alternate, and whether or not this data is inaccessible to 3rd events.
And the truth that IIoT safety audits stretch far past figuring out {hardware} options by their IP and working system solely complicates the matter.
Resolution
There are a number of steps you could possibly take to realize machine and community visibility in IIoT deployments:
- Analyze all community communications utilizing deep packet inspection (DPI) options
- Gather exhaustive machine data, together with {hardware} sort, mannequin, serial quantity, and embedded system variations
- Group your units based mostly on their sort, perform, mission criticality, and potential IIoT safety dangers
- Create digital native space networks (VLANs) for each machine group to reinforce site visitors visibility and management
- Make use of dependable machine administration platforms, equivalent to AWS IoT Core, Azure IoT Hub, and PTC ThingWorks, to enhance machine inventories, monitoring, configuration, replace rollouts, and troubleshooting
Problem #5: Inadequate worker coaching and cyber-awareness
As we have talked about earlier, an absence of collaboration and coordination between data expertise (IT) and operational expertise (OT) groups may end up in poor IIoT safety administration practices.
Whereas gear operators and manufacturing unit managers correctly take care of linked machines, they know little concerning the embedded and connectivity applied sciences that energy them. IT groups, quite the opposite, are well-versed in conventional data safety however are likely to deal with IIoT options like extraordinary {hardware}.
This will result in low patch ranges, restricted visibility into community exercise, and misconfigurations of the Industrial Web of Issues techniques. Moreover, cybercriminals might exploit your worker’s restricted data of IIoT safety greatest practices by phishing assaults and impersonation. Your staff can also select weak passwords or reuse passwords throughout purposes, which can open a backdoor to your IT infrastructure, undermining IIoT software program safety.
Resolution
Here is a high-level plan that might assist your organization elevate cybersecurity consciousness amongst staff:
- Create coaching packages particularly tailor-made to the Industrial IoT atmosphere. These packages ought to cowl subjects equivalent to cybersecurity fundamentals, IoT machine safety, safe configuration practices, password hygiene, recognizing and reporting potential safety incidents, and compliance with inner safety insurance policies and procedures.
- Conduct common coaching classes to make sure staff keep up-to-date with the most recent cybersecurity threats and greatest practices. This may be achieved by workshops, seminars, webinars, or on-line coaching modules in your studying administration system (LMS). As a part of the coaching actions, as an example, you could possibly educate your employees to acknowledge and reply to IIoT safety threats by phishing simulations and penetration testing. You also needs to tailor coaching packages to particular job capabilities, making certain that staff obtain the coaching related to their tasks. For instance, IT employees might require extra technical coaching, whereas operational staff may have coaching on safe machine utilization and bodily safety.
- Develop complete insurance policies and procedures that handle the distinctive Industrial Web of Issues safety challenges. Talk these insurance policies successfully to staff and guarantee they perceive their roles and tasks in sustaining safety. Usually overview and replace these insurance policies as expertise and threats evolve.
- Promote a tradition of IIoT safety consciousness and accountability all through the group. Encourage staff to report any safety incidents or suspicious actions promptly. Emphasize that cybersecurity is everybody’s duty, from prime administration to frontline employees, and reward staff for demonstrating good safety practices.
- Take into account partnering with exterior Industrial IoT specialists or consultants to conduct safety assessments. Exterior specialists can deliver helpful insights, trade greatest practices, and the most recent risk intelligence to reinforce worker coaching packages. Moreover, they may aid you deliver the so-called “safety by design” practices into the IIoT software program growth course of and elicit practical and non-functional necessities for IIoT deployments.
On a closing notice
IIoT adoption charges have soared lately – and so have the high-profile assaults focusing on vital IIoT infrastructures within the industrial section.
Based on a current survey from Examine Level, within the first two months of 2023, 54% of corporations suffered IoT-related assaults, with an estimated 60 assaults per week per group (41% up from final yr). Among the many units most vulnerable to hacker assaults had been routers, community video recorders, and IP cameras – briefly, {hardware} that includes the spine of each firm’s IT infrastructure.
Even when your IT staff follows IIoT safety greatest practices all through the event and implementation course of, there isn’t any assure hackers will not train management over your gear and information by exploiting vulnerabilities in apps and units outdoors the IIoT ecosystem. That is why your organization wants an all-embracing safety technique – and this is what ITRex can do for you!
Whether or not you are contemplating launching an IIoT pilot or need assistance scaling an Industrial IoT proof of idea (PoC) throughout different use circumstances, drop us a line! We’re well-versed in enterprise evaluation, embedded system engineering, cloud computing and DevOps, and end-user software growth.
The put up IIoT Safety Challenges & Tricks to Navigate Them appeared first on Datafloq.

