Targets situated in Azerbaijan have been singled out as a part of a brand new marketing campaign that is designed to deploy Rust-based malware on compromised techniques.
Cybersecurity agency Deep Intuition is monitoring the operation underneath the identify Operation Rusty Flag. It has not been related to any identified risk actor or group.
“The operation has no less than two totally different preliminary entry vectors,” safety researchers Simon Kenin, Ron Ben Yizhak, and Mark Vaitzman stated in an evaluation printed final week. “One of many lures used within the operation is a modified doc that was utilized by the Storm-0978 group. This may very well be a deliberate ‘false flag.'”

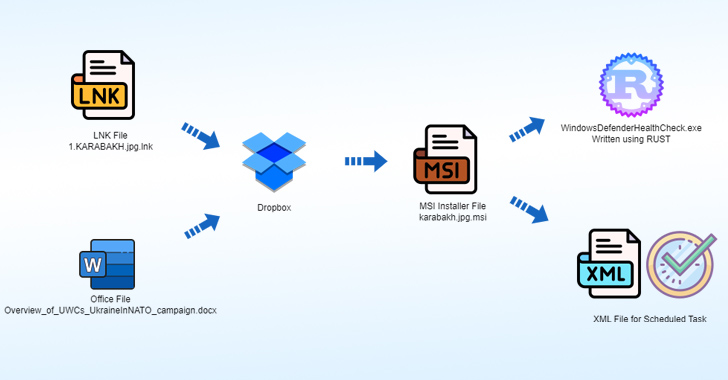
The assault chain leverages an LNK file named 1.KARABAKH.jpg.lnk as a launchpad to retrieve a second-stage payload, an MSI installer, hosted on Dropbox.
The installer file, for its half, drops an implant written in Rust, an XML file for a scheduled process to execute the implant, and a decoy picture file that options watermarks of the image of the Azerbaijan Ministry of Protection.
An alternate an infection vector is a Microsoft Workplace doc named “Overview_of_UWCs_UkraineInNATO_campaign.docx,” which exploits CVE-2017-11882, a six-year-old reminiscence corruption vulnerability in Microsoft Workplace’s Equation Editor, to invoke a Dropbox URL internet hosting a unique MSI file serving a variant of the identical Rust backdoor.
Using Overview_of_UWCs_UkraineInNATO_campaign.docx is noteworthy, as a lure with the identical filename was leveraged by Storm-0978 (aka RomCom, Tropical Scorpius, UNC2596, and Void Rabisu) in current cyber assaults focusing on Ukraine that exploit an Workplace distant code execution flaw (CVE-2023-36884).
Degree-Up SaaS Safety: A Complete Information to ITDR and SSPM
Keep forward with actionable insights on how ITDR identifies and mitigates threats. Be taught concerning the indispensable function of SSPM in making certain your identification stays unbreachable.
“This motion seems to be like a deliberate false flag try to pin this assault on Storm-0978,” the researchers stated.
The Rust backdoor, certainly one of which masquerades as “WinDefenderHealth.exe,” comes fitted with capabilities to assemble data from the compromised host and ship it to an attacker-controlled server.
The precise finish targets of the marketing campaign stay unclear at this stage. On the identical time, the chance that it may very well be a pink group train has not been discounted.
“Rust is gaining popularity amongst malware authors,” the researchers stated. “Safety merchandise will not be but detecting Rust malware precisely, and the reverse engineering course of is extra advanced.”