The current assault towards Microsoft’s e mail infrastructure by a Chinese language nation-state actor known as Storm-0558 is alleged to have a broader scope than beforehand thought.
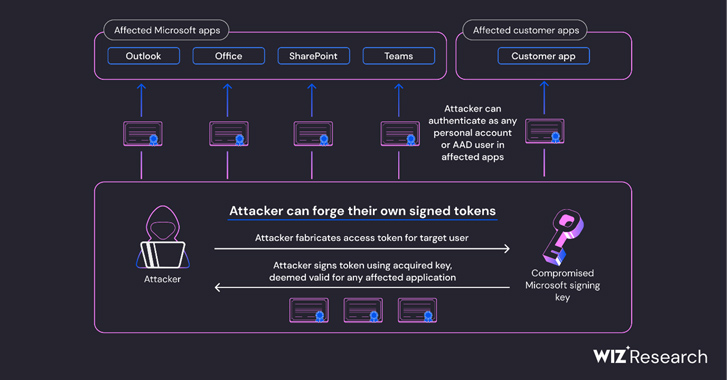
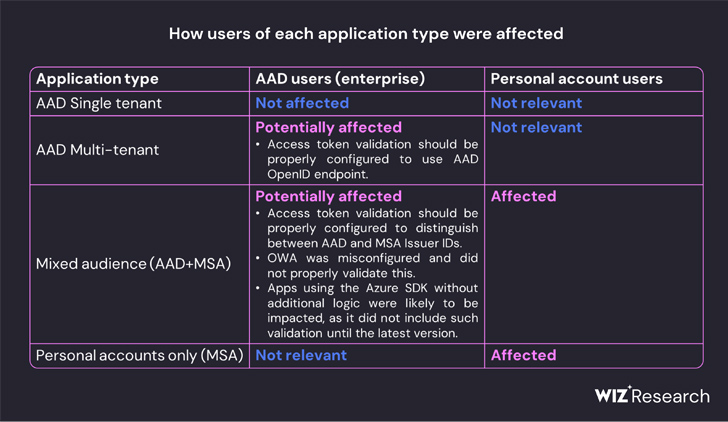
In response to cloud safety firm Wiz, the inactive Microsoft account (MSA) shopper signing key used to forge Azure Energetic Listing (Azure AD or AAD) tokens to realize illicit entry to Outlook Net Entry (OWA) and Outlook.com might even have allowed the adversary to forge entry tokens for varied sorts of Azure AD functions.
This contains each utility that helps private account authentication, akin to OneDrive, SharePoint, and Groups; clients functions that assist the “Login with Microsoft performance,” and multi-tenant functions in sure circumstances.
“All the pieces on the earth of Microsoft leverages Azure Energetic Listing auth tokens for entry,” Ami Luttwak, chief expertise officer and co-founder of Wiz, mentioned in a press release. “An attacker with an AAD signing secret is probably the most highly effective attacker you’ll be able to think about, as a result of they’ll entry virtually any app – as any person. It is a ‘form shifter’ superpower.”
Microsoft, final week, disclosed the token forging method was exploited by Storm-0558 to extract unclassified information from sufferer mailboxes, however the precise contours of the cyber espionage marketing campaign stays unknown.
The Home windows maker mentioned it is nonetheless investigating as to how the adversary managed to accumulate the MSA shopper signing key. However it’s unclear if the important thing functioned as a grasp key of kinds to unlock entry to information belonging to just about two dozen organizations.
Wiz’s evaluation fills in among the blanks, with the corporate discovering that “all Azure private account v2.0 functions depend upon an inventory of 8 public keys, and all Azure multi-tenant v2.0 functions with Microsoft account enabled depend upon an inventory of 7 public keys.”
It additional discovered that Microsoft changed one of many the listed public keys (thumbprint: “d4b4cccda9228624656bff33d8110955779632aa”) that had been current since not less than 2016 someday between June 27, 2023, and July 5, 2023, across the identical interval the corporate mentioned it had revoked the MSA key.
“This led us to consider that though the compromised key acquired by Storm-0558 was a personal key designed for Microsoft’s MSA tenant in Azure, it was additionally capable of signal OpenID v2.0 tokens for a number of sorts of Azure Energetic Listing functions,” Wiz mentioned.
Defend Towards Insider Threats: Grasp SaaS Safety Posture Administration
Apprehensive about insider threats? We have you coated! Be part of this webinar to discover sensible methods and the secrets and techniques of proactive safety with SaaS Safety Posture Administration.
“Storm-0558 seemingly managed to acquire entry to certainly one of a number of keys that had been meant for signing and verifying AAD entry tokens. The compromised key was trusted to signal any OpenID v2.0 entry token for private accounts and mixed-audience (multi-tenant or private account) AAD functions.”
This successfully implies that it might theoretically allow malicious actors to forge entry tokens for consumption by any utility that relies on the Azure id platform.
Even worse, the acquired personal key might have been weaponized to forge tokens to authenticate as any person to an affected utility that trusts Microsoft OpenID v2.0 combined viewers and personal-accounts certificates.
“Id supplier’s signing keys are in all probability probably the most highly effective secrets and techniques within the fashionable world,” Wiz safety researcher Shir Tamari mentioned. “With id supplier keys, one can acquire quick single hop entry to the whole lot, any e mail field, file service, or cloud account.”