The risk actors behind RedLine and Vidar info stealers have been noticed pivoting to ransomware by phishing campaigns that unfold preliminary payloads signed with Prolonged Validation (EV) code signing certificates.
“This means that the risk actors are streamlining operations by making their methods multipurpose,” Development Micro researchers stated in a brand new evaluation printed this week.
Within the incident investigated by the cybersecurity firm, an unnamed sufferer is claimed to have first acquired a chunk of information stealer malware with EV code signing certificates, adopted by ransomware utilizing the identical supply approach.
Previously, QakBot infections have leveraged samples signed with legitimate code signing certificates to bypass safety protections.
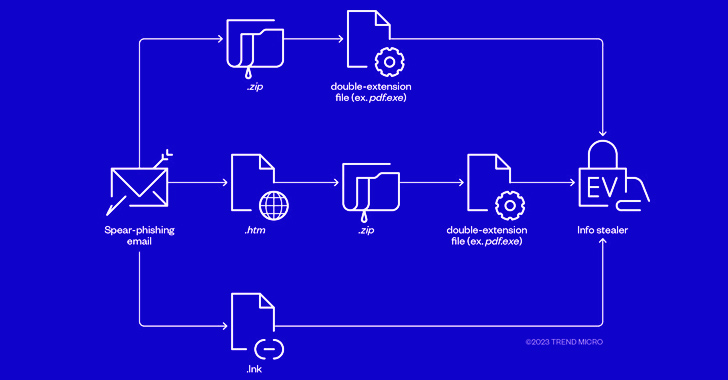
The assaults begin with phishing emails that make use of well-worn lures to trick victims into working malicious attachments that masquerade as PDF or JPG pictures however are literally executables that jump-start the compromise upon working.

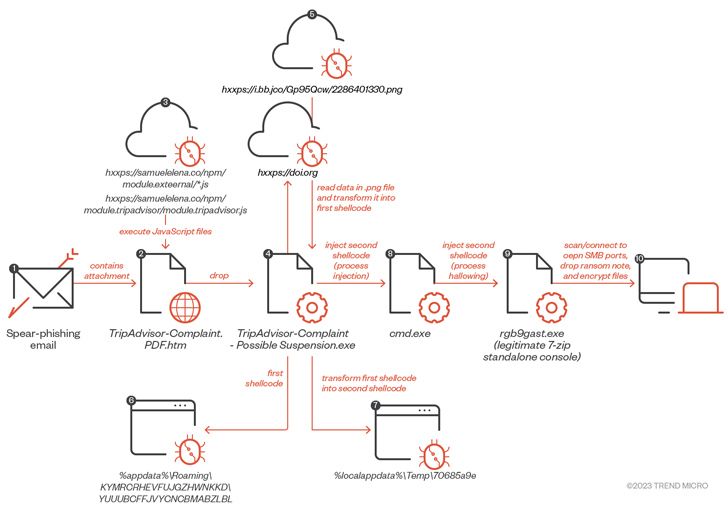
Whereas the marketing campaign focusing on the sufferer delivered stealer malware in July, a ransomware payload made its manner in early August after receiving an e-mail message containing a bogus TripAdvisor grievance e-mail attachment (“TripAdvisor-Grievance.pdf.htm”), triggering a sequence of steps that culminated within the deployment of ransomware.
“At this level, it’s price noting that in contrast to the samples of the data stealer we investigated, the recordsdata used to drop the ransomware payload didn’t have EV certificates,” the researchers stated.
“Nonetheless, the 2 originate from the identical risk actor and are unfold utilizing the identical supply methodology. We will due to this fact assume a division of labor between the payload supplier and the operators.”
The event comes as IBM X-Drive found new phishing campaigns spreading an improved model of a malware loader named DBatLoader, which was used as a conduit to distribute FormBook and Remcos RAR earlier this yr.
DBatLoader’s new capabilities facilitate UAC bypass, persistence, and course of injection, indicating that it is being actively maintained to drop malicious applications that may accumulate delicate info and allow distant management of programs.
The current set of assaults, detected since late June, are engineered to additionally ship commodity malware reminiscent of Agent Tesla and Warzone RAT. A majority of the e-mail messages have singled out English audio system, though emails in Spanish and Turkish have additionally been noticed.
“In a number of noticed campaigns the risk actors leveraged ample management over the e-mail infrastructure to allow malicious emails to cross SPF, DKIM, and DMARC e-mail authentication strategies,” the corporate stated.
“A majority of campaigns leveraged OneDrive to stage and retrieve further payloads, with a small fraction in any other case using switch[.]sh or new/compromised domains.”
Identification is the New Endpoint: Mastering SaaS Safety within the Trendy Age
Dive deep into the way forward for SaaS safety with Maor Bin, CEO of Adaptive Protect. Uncover why id is the brand new endpoint. Safe your spot now.
In associated information, Malwarebytes revealed {that a} new malvertising marketing campaign is focusing on customers who’re looking for Cisco’s Webex video conferencing software program on engines like google like Google to redirect them to a pretend web site that propagates the BATLOADER malware.
BATLOADER, for its half, establishes contact with a distant server to obtain a second-stage encrypted payload, which is one other recognized stealer and keylogger malware known as DanaBot.
A novel approach adopted by the risk actor is using monitoring template URLs as a filtering and redirection mechanism to fingerprint and decide potential victims of curiosity. Guests who do not meet the factors (e.g., requests originating from a sandboxed setting) are directed to the reputable Webex web site.
“As a result of the adverts look so reputable, there’s little doubt individuals will click on on them and go to unsafe websites,” Jérôme Segura, director of risk intelligence at Malwarebytes, stated.
“The kind of software program being utilized in these adverts point out that risk actors are taken with company victims that may present them with credentials helpful for additional community ‘pentesting’ and, in some circumstances, ransomware deployment.”