
The Europol report reported on cybercriminals’ use of cryptocurrencies and the way their methods are extra subtle. Nevertheless, there was good cybersecurity information, too.
Europol, the European Union’s company for regulation enforcement cooperation, launched its yearly Web Organised Crime Risk Evaluation report, which offers key findings and rising cybersecurity threats that affect governments, companies and people in Europe; nonetheless, these threats can have an effect on folks worldwide. The principle themes of the report are cybercriminals are more and more codependent, the basics of cybercrime, technically talking, stay the identical and there’s a fixed use of cryptocurrencies and an elevated use of mixers.
Leap to:
Enhance in cybercriminals’ experience makes them extra codependent
In line with Europol, the panorama of cybercrime has developed into a posh internet of interdependence amongst cybercriminals.
As pc safety and protection evolves, cybercrime does, too. Various kinds of pc data are wanted for working fraud on the web. As an illustration, relying on the fraud, a cybercriminal would possibly want malware that isn’t detected by antivirus and safety options, a safe web connection that may’t be traced again to them, preliminary entry to corporations’ networks or mailboxes, environment friendly social engineering content material, fraudulent content material internet hosting and extra.
All of these wants require deep data in numerous fields, which is a motive why a variety of cybercriminals have determined to promote their data as a service to different cybercriminals.
Preliminary entry brokers promote the compromised accesses they gather to different cybercriminals who use it for on-line fraud schemes. IABs are additionally “pivotal for ransomware assaults,” wrote Europol, as they promote preliminary entry to ransomware teams who then use it to penetrate company programs to maneuver inside their community earlier than executing the ransomware.
Crypter builders conceal malicious payloads and malware so that they’re tougher for safety options to detect.
Counter AntiVirus providers are very talked-about amongst cybercriminals. Malware builders and crypter providers frequently use CAV providers to scan their binaries in opposition to a number of antivirus options. This permits them to determine which components of their code are flagged as malicious by antivirus engines.
Digital personal networks are supplied by cybercriminals to keep away from identification. A number of VPN options can be found within the cybercriminal underground market, providing anonymity by encrypting site visitors from end-to-end and by not offering any cooperation with requests for info from regulation enforcement entities.
Bulletproof internet hosting is central to quite a lot of cybercrimes and is utilized by many criminals. Europol acknowledged that these internet hosting providers “… don’t have interaction in in depth buyer monitoring practices comparable to Know-Your-Buyer procedures and storing of buyer and metadata facilitating felony actions.” Bulletproof internet hosting providers don’t present buyer info to regulation enforcement aside from an automatic affirmation of an e-mail deal with. Lastly, internet hosting issues might be troublesome, because it’s typically a posh worldwide enterprise the place servers are sometimes in a number of areas worldwide.
Andy Zollo, regional vice chairman for EMEA at cybersecurity firm Imperva, talked with TechRepublic.
“The truth that so many cybercriminals at the moment are working co-dependent providers is additional proof of how advanced the cybercrime business has turn out to be, and demonstrates the necessity for organisations to have cohesive safety methods in place that may defend functions, APIs, and their delicate information. Nevertheless, the flip facet is that the rising co-dependency amongst cybercriminals implies that if companies are in a position to disrupt any a part of the cybercrime provide chain, it will probably make a big distinction to their general safety posture. Even one answer or initiative, if well-targeted, might be sufficient to assist break the cycle.”
Modus operandi doesn’t change, methods improve in sophistication
All varieties of cybercriminals use the identical strategies of reaching their targets in some unspecified time in the future. Probably the most used method is phishing; it’s typically all the time the place to begin of monetary fraud or cyberespionage operations.
From a technical standpoint, the modus opérandi doesn’t change, however the best way to realize it will get extra subtle and will increase in quantity. European Union regulatory developments have made fraud with compromised bank card info tougher, which has the impact of turning cybercriminals extra onto the customers than the digital programs.
Distant Desktop Protocol brute-forcing and VPN vulnerability exploitation are the most typical intrusion techniques utilized by cybercriminals, in line with Europol. Phishing kits have additionally turn out to be more and more out there for cybercriminals, no matter their degree of group and technical experience.
SEE: TechRepublic Premium’s Brute Power and Dictionary Assaults: A Information for IT Leaders
Obfuscated cryptocurrencies actions
When potential, cybercriminals use cryptocurrencies. Ransomware teams all request cryptocurrencies, paid instantly on devoted crypto wallets. Funds between cybercriminals for various providers are additionally all the time made in cryptocurrencies.
An intensive use of a number of layers of obfuscation methods is mostly deployed by cybercriminals earlier than lastly cashing out their unlawful income. Cryptocurrency mixers, a service that blends the cryptocurrencies of many customers collectively, are sometimes used to obfuscate the origins and homeowners of the funds. These mixers make it troublesome for investigators to hint the cash trails successfully.
One other generally employed methodology is cryptocurrency swappers, which permit for fast buying and selling from one cryptocurrency to a different, additional complicating the method of figuring out the origin of the funds. As well as, change of nations and decentralized exchanges are used for obfuscation. These cryptocurrency obfuscation methods require extremely expert investigators to observe the cash trails and conduct profitable investigations.
Europol exhibits a posh cryptocurrency case the place mixers, cryptocurrency switches and splits are closely used (Determine A).
Determine A
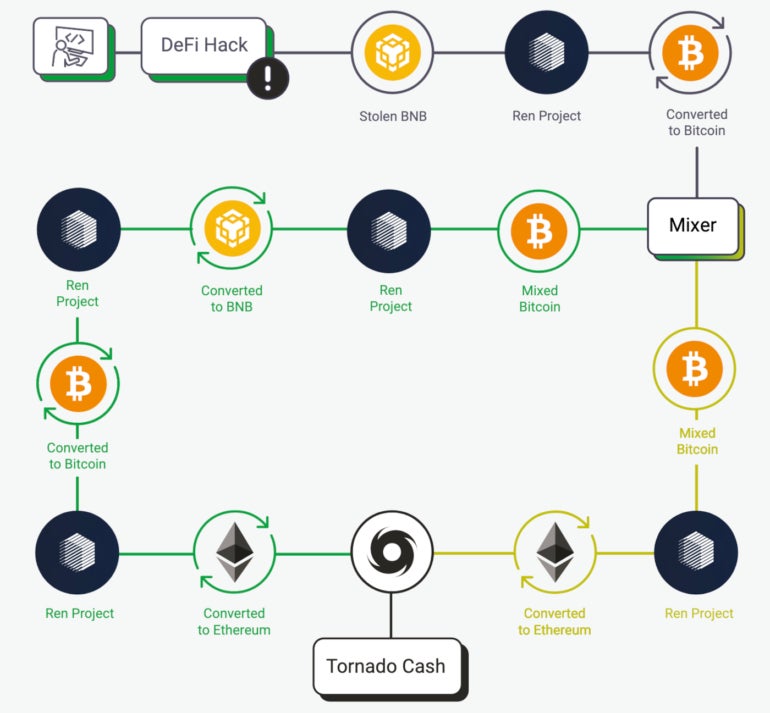
Within the Decentralised Finance hack depicted in Determine A, the cryptocurrency, Binance Coin, is stolen and despatched to Ren Venture, a protocol that permits motion of values throughout blockchains. Then, it’s transformed to Bitcoin earlier than going right into a mixer that splits the cash in two, going again to Ren Venture. It’s transformed to BNB on one facet and transformed to Ethereum on the opposite facet. The Ethereum quantity goes by the Twister Money mixer earlier than being reconverted to Ethereum.
Excellent news for preventing cybercrime
The time when a cybercriminal was working all of their fraud alone is coming to an finish; cybercriminals need to be environment friendly, so that they purchase the providers of extra expert friends slightly than do it themselves. That is excellent news for the struggle in opposition to cybercrime as a result of arresting cybercriminals on one facet of cybercrime typically impacts others and stops much more fraud.
For instance, Europol reported a number of profitable worldwide operations resulting in arrests. One occasion was the VPNLab takedown in 2022. Many customers of VPNLab used the service to connect with domains of corporations being compromised by a ransomware group. This takedown demonstrated how bringing down one service may assist additional investigations.
One other instance is Operation Elaborate in 2022, which took down a full service that supplied Automated Interactive Voice Response, interception of one-time passwords and dwell monitoring of calls, resulting in the arrest of 142 suspects.
Disclosure: I work for Pattern Micro, however the views expressed on this article are mine.

