Telephones, tablets and workstations with unpatched CVEs are a transparent and current hazard. New Armis examine lists essentially the most susceptible.
Asset visibility and safety firm Armis recognized related property posing the best dangers to world enterprise. Armis’ new analysis, primarily based on evaluation from its Asset Intelligence Engine, targeted on related property with essentially the most assault makes an attempt, weaponized frequent vulnerabilities and exposures and different high-risk elements.
Most susceptible property included IoT, IT, constructing administration
The highest 10 asset varieties with the very best variety of assault makes an attempt had been distributed throughout IT, operational expertise, the Web of Issues, the Web of Medical Issues, the Web of Private Issues and constructing administration techniques.
SEE: Securing IoT with Microsoft Defender for IoT sensors (TechRepublic)
Armis reported that the units with the very best variety of assault makes an attempt had been:
- Engineering workstations (OT).
- Imaging workstations (IoMT).
- Media gamers (IoT).
- Private computer systems (IT).
- Digital machines (IT).
- Uninterruptible energy provide (UPS) units (BMS).
- Servers (IT).
- Media writers (IoMT).
- Tablets (IoPT).
- Cell phones (IoPT).
The analysis reiterates findings in June this yr in regards to the most at-risk units by the agency’s Asset Intelligence and Safety Platform, which tracks over 3 billion property in line with Armis.
In that analysis, Armis discovered essential vulnerabilities in engineering workstations, supervisory management and information acquisition servers, automation servers, management system historians and programmable logic controllers, that are additionally essentially the most susceptible OT and industrial management techniques.
“Malicious actors are deliberately concentrating on these property as a result of they’re externally accessible, have an expansive and complicated assault floor and recognized weaponized CVEs,” mentioned Tom Gol, CTO of analysis at Armis.
Gol mentioned in an announcement that these property are engaging for attackers as a result of they will wreak havoc throughout a number of techniques.
SEE: Armis and Honeywell uncover vulnerabilities in Honeywell Methods (TechRepublic)
“Engineering workstations might be related to all controllers in a manufacturing unit, imaging workstations will accumulate personal affected person information from hospitals and UPSs can function an entry level to essential infrastructure entities, making all of those engaging targets for malicious actors with various agendas, like deploying ransomware or inflicting destruction to society within the case of nation-state assaults,” Gol mentioned, including that defenders ought to enhance visibility of those property and patch vulnerabilities (Determine A).
Determine A
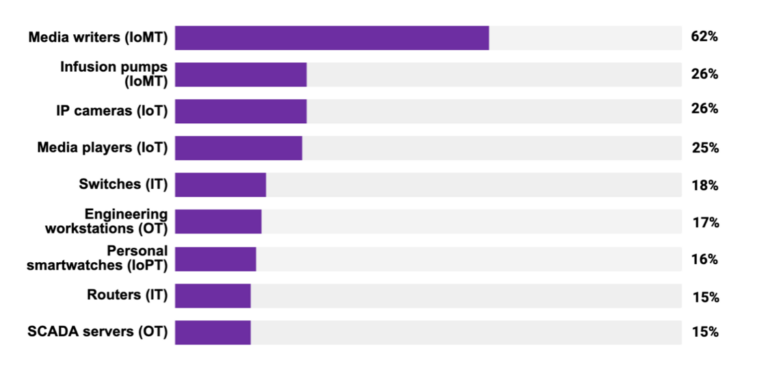
Excessive-risk elements for frequent {hardware} and techniques
The Armis researchers discovered a lot of asset varieties with frequent high-risk elements:
- Servers and programmable logic controllers constituting end-of-life or end-of-support working techniques.
- Private computer systems and the like utilizing SMBv1, a posh and unencrypted protocol. These vulnerabilities, together with EternalBlue, had been exploited by WannaCry and NotPetya assaults.
- Belongings with excessive vulnerability scores or which have had threats detected or have been flagged for unencrypted site visitors or that also have the CDPwn vulnerabilities impacting community infrastructure and VoIPs.
- Half of pneumatic tube techniques have an unsafe software program replace mechanism.
Armis mentioned it discovered that 74% of organizations immediately nonetheless have a minimum of one asset of their community susceptible to EternalBlue exploited by NotPetya to realize preliminary entry earlier than utilizing credential theft for privilege escalation.
“Persevering with to coach world companies in regards to the evolving and elevated danger being launched to their assault floor by managed and unmanaged property is a key mission of ours,” mentioned Nadir Izrael, CTO and cofounder of Armis. “This intelligence is essential to serving to organizations defend towards malicious cyberattacks. With out it, enterprise, safety and IT leaders are at midnight, susceptible to blind spots that unhealthy actors will search to take advantage of.”