We discovered some exceptional new particulars this week concerning the latest supply-chain assault on VoIP software program supplier 3CX. The prolonged, complicated intrusion has all of the makings of a cyberpunk spy novel: North Korean hackers utilizing legions of pretend govt accounts on LinkedIn to lure folks into opening malware disguised as a job provide; malware focusing on Mac and Linux customers working at protection and cryptocurrency corporations; and software program supply-chain assaults nested inside earlier provide chain assaults.
Researchers at ESET say this job provide from a phony HSBC recruiter on LinkedIn was North Korean malware masquerading as a PDF file.
In late March 2023, 3CX disclosed that its desktop functions for each Home windows and macOS had been compromised with malicious code that gave attackers the power to obtain and run code on all machines the place the app was put in. 3CX says it has greater than 600,000 clients and 12 million customers in a broad vary of industries, together with aerospace, healthcare and hospitality.
3CX employed incident response agency Mandiant, which launched a report on Wednesday that mentioned the compromise started in 2022 when a 3CX worker put in a malware-laced software program bundle distributed by way of an earlier software program provide chain compromise that started with a tampered installer for X_TRADER, a software program bundle offered by Buying and selling Applied sciences.
“That is the primary time Mandiant has seen a software program provide chain assault result in one other software program provide chain assault,” reads the April 20 Mandiant report.
Mandiant discovered the earliest proof of compromise uncovered inside 3CX’s community was by the VPN utilizing the worker’s company credentials, two days after the worker’s private laptop was compromised.
“Ultimately, the risk actor was capable of compromise each the Home windows and macOS construct environments,” 3CX mentioned in an April 20 replace on their weblog.
Mandiant concluded that the 3CX assault was orchestrated by the North Korean state-sponsored hacking group referred to as Lazarus, a willpower that was independently reached earlier by researchers at Kaspersky Lab and Elastic Safety.
Mandiant discovered the compromised 3CX software program would obtain malware that sought out new directions by consulting encrypted icon information hosted on GitHub. The decrypted icon information revealed the placement of the malware’s management server, which was then queried for a 3rd stage of the malware compromise — a password stealing program dubbed ICONICSTEALER.
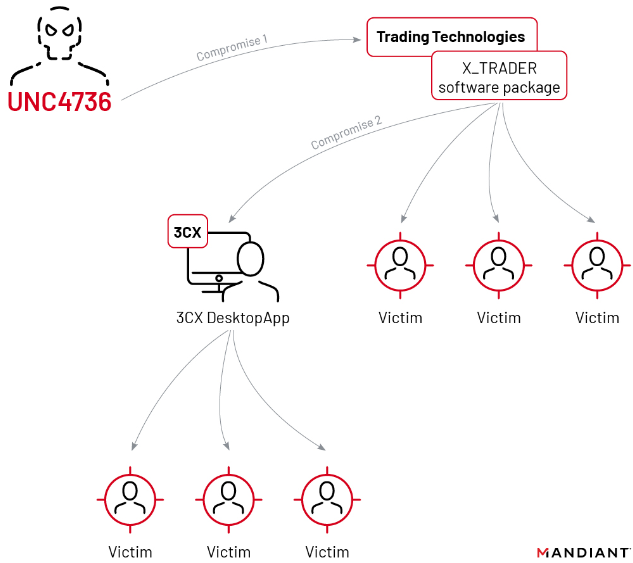
The double provide chain compromise that led to malware being pushed out to some 3CX clients. Picture: Mandiant.
In the meantime, the safety agency ESET at present revealed analysis displaying exceptional similarities between the malware used within the 3CX provide chain assault and Linux-based malware that was not too long ago deployed by way of pretend job presents from phony govt profiles on LinkedIn. The researchers mentioned this was the primary time Lazarus had been noticed deploying malware geared toward Linux customers.
As reported in a collection final summer season right here, LinkedIn has been inundated this previous 12 months by pretend govt profiles for folks supposedly employed at a spread of know-how, protection, power and monetary firms. In lots of instances, the phony profiles spoofed chief data safety officers at main companies, and a few attracted fairly just a few connections earlier than their accounts had been terminated.
Mandiant, Proofpoint and different consultants say Lazarus has lengthy used these bogus LinkedIn profiles to lure targets into opening a malware-laced doc that’s usually disguised as a job provide. This ongoing North Korean espionage marketing campaign utilizing LinkedIn was first documented in August 2020 by ClearSky Safety, which mentioned the Lazarus group operates dozens of researchers and intelligence personnel to take care of the marketing campaign globally.
Microsoft Corp., which owns LinkedIn, mentioned in September 2022 that it had detected a variety of social engineering campaigns utilizing a proliferation of phony LinkedIn accounts. Microsoft mentioned the accounts had been used to impersonate recruiters at know-how, protection and media firms, and to entice folks into opening a malicious file. Microsoft discovered the attackers usually disguised their malware as professional open-source software program like Sumatra PDF and the SSH shopper Putty.
Microsoft attributed these assaults to North Korea’s Lazarus hacking group, though they’ve historically referred to this group as “ZINC“. That’s, till earlier this month, when Redmond fully revamped the way in which it names risk teams; Microsoft now references ZINC as “Diamond Sleet.”
The ESET researchers mentioned they discovered a brand new pretend job lure tied to an ongoing Lazarus marketing campaign on LinkedIn designed to compromise Linux working techniques. The malware was discovered within a doc that provided an employment contract on the multinational financial institution HSBC.
“Just a few weeks in the past, a local Linux payload was discovered on VirusTotal with an HSBC-themed PDF lure,” wrote ESET researchers Peter Kalnai and Marc-Etienne M.Leveille. “This completes Lazarus’s skill to focus on all main desktop working techniques. On this case, we had been capable of reconstruct the complete chain, from the ZIP file that delivers a pretend HSBC job provide as a decoy, up till the ultimate payload.”
ESET mentioned the malicious PDF file used within the scheme appeared to have a file extension of “.pdf,” however that this was a ruse. ESET found that the dot within the filename wasn’t a standard interval however as an alternative a Unicode character (U+2024) representing a “chief dot,” which is commonly utilized in tables of contents to attach part headings with the web page numbers on which these sections start.
“Using the chief dot within the filename was in all probability an try and trick the file supervisor into treating the file as an executable as an alternative of a PDF,” the researchers continued. “This might trigger the file to run when double-clicked as an alternative of opening it with a PDF viewer.”
ESET mentioned anybody who opened the file would see a decoy PDF with a job provide from HSBC, however within the background the executable file would obtain further malware payloads. The ESET staff additionally discovered the malware was capable of manipulate this system icon displayed by the malicious PDF, presumably as a result of twiddling with the file extension may trigger the consumer’s system to show a clean icon for the malware lure.
Kim Zetter, a veteran Wired.com reporter and now impartial safety journalist, interviewed Mandiant researchers who mentioned they count on “many extra victims” will likely be found among the many clients of Buying and selling Applied sciences and 3CX now that information of the compromised software program packages is public.
“Mandiant knowledgeable Buying and selling Applied sciences on April 11 that its X_Trader software program had been compromised, however the software program maker says it has not had time to research and confirm Mandiant’s assertions,” Zetter wrote in her Zero Day e-newsletter on Substack. For now, it stays unclear whether or not the compromised X_Trader software program was downloaded by folks at different software program corporations.
If there’s a silver lining right here, the X_Trader software program had been decommissioned in April 2020 — two years earlier than the hackers allegedly embedded malware in it.
“The corporate hadn’t launched new variations of the software program since that point and had stopped offering assist for the product, making it a less-than-ideal vector for the North Korean hackers to contaminate clients,” Zetter wrote.
