Analysis and growth of quantum computer systems continues to develop at a fast tempo. The U.S. authorities alone spent greater than $800 million on quantum info science (QIS) analysis in 2022. The promise of quantum computer systems is substantial – they are going to have the ability to remedy sure issues which are classically intractable, that means a traditional laptop can’t full the calculations inside human-usable timescales. Given this computational energy, there may be rising dialogue surrounding the cyber threats quantum computer systems could pose sooner or later. As an example, Alejandro Mayorkas, secretary of the Division of Homeland Safety, has recognized the transition to post-quantum encryption as a precedence to make sure cyber resilience. There may be little or no dialogue, nevertheless, on how we’ll defend quantum computer systems sooner or later. If quantum computer systems are to grow to be such useful belongings, it’s affordable to mission that they are going to ultimately be the goal of malicious exercise.
I used to be lately invited to be a participant within the Workshop on Cybersecurity of Quantum Computing, co-sponsored by the Nationwide Science Basis (NSF) and The White Home Workplace of Science and Expertise Coverage, the place we examined the rising discipline of cybersecurity for quantum computing. Whereas quantum computer systems are nonetheless nascent in some ways, it’s by no means too early to handle looming cybersecurity considerations. This publish will discover points associated to creating the self-discipline of cyber safety of quantum computing and description six areas of future analysis within the discipline of quantum cybersecurity.
What’s Quantum Computing?
The frequent computer systems that most individuals use day-after-day are constructed on the binary logic of bits, that are primarily based on 0 and 1 as represented by a binary bodily property, equivalent to whether or not circulation of electrical energy to a transistor is off or on. These conventional computer systems are usually known as classical computer systems when mentioned in relation to quantum computer systems. In distinction to the binary nature of classical computer systems, quantum computer systems use qubits, that are able to being in a superposition of two states on the identical time (i.e., representing each a 0 and 1 on the identical time). One analogy to understanding superposition is to think about flipping a coin. A classical laptop can signify the coin as being heads or tails after the coin lands. A quantum laptop, alternatively, can signify the coin as each heads and tails on the identical time whereas it’s nonetheless flipping within the air.
The aptitude of quantum computer systems is additional enriched by the property of entanglement, which permits distributed encoding of data. Quantum entanglement permits qubits which are separated, even by vital distances, to work together with one another instantaneously. Entanglement happens when particles work together in such a manner that every particle’s quantum state can’t be described independently of the state of the others. That’s, the measured states of entangled particles are correlated such that measurement of state for a single particle permits probabilistic prediction of state for others. Think about the coin flipping instance from above; now think about that two cash are flipped on the identical time. As they’re flipping within the air, the states of every coin are correlated.
Collectively, quantum superposition and entanglement allow substantial computing energy. Think about {that a} 2-bit register in a classical laptop can retailer solely one of 4 binary mixtures (00, 01, 10, or 11) at a given time, however a 2-qubit register in a quantum laptop can retailer all 4 of those numbers concurrently. As extra qubits are added, this computational benefit of quantum computer systems over classical computer systems grows exponentially.
Cyber Threats to Quantum Computer systems
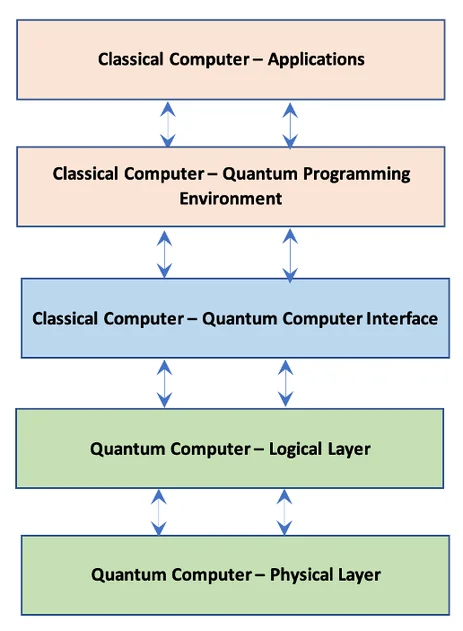
The present state of quantum laptop programs is also known as the NISQ (noisy intermediate-scale quantum) period, characterised by quantum computer systems that provide average computing energy and are nonetheless challenged by system constancy. Present quantum computer systems are unstable and unstable, with error-correction for quantum calculations nonetheless being addressed. Whereas researchers work to unravel these challenges, it’s obvious that within the near-term—and additional into the near-future—quantum computer systems will more than likely be used as co-processors in hybrid programs during which classical computer systems will hand off mathematical calculations to the quantum laptop as half of a bigger system workflow that also closely is dependent upon classical computer systems. The diagram under exhibits a notional idea of the elements for a quantum-classical hybrid comuting atmosphere. Implementation particulars will range by quantum architectures, however comparable layers will exist in all quantum-classical hybrid computer systems.
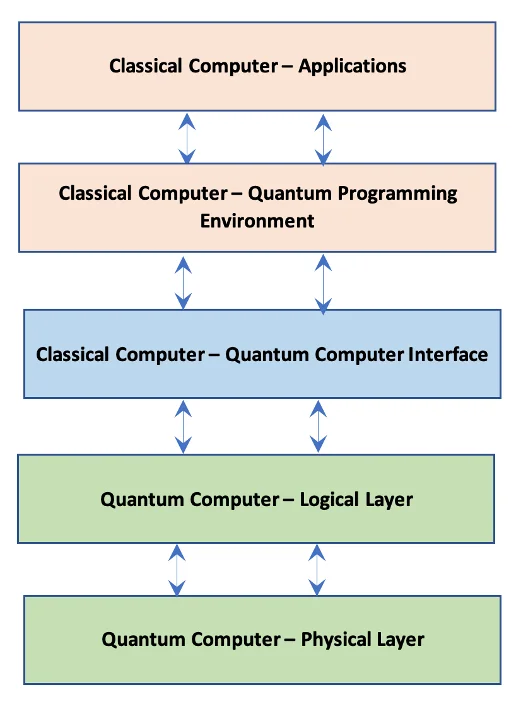
Determine 1: Notional Mannequin of Classical-Quantum Hybrid Pc
Understanding how quantum computer systems can be built-in with classical computer systems is crucial to contemplating the cyber threats to quantum computer systems. The interface between classical and quantum computer systems within the hybrid computing environments typical of the NISQ-era is an space ripe for cybersecurity threats. This interface is actually the gateway between the classical and quantum environments, so it could function a conduit for recognized exploits of classical computer systems to traverse into quantum areas. Briefly, there are already many recognized cyber assault methods for classical computer systems that may be leveraged to compromise a hybrid system.
One other assault vector stems from novel approaches for management and measurement of quantum units that can be applied in these interfaces. Software-specific built-in circuits (ASICs), field-programmable gate arrays (FPGAs), digital-to-analogue converters (DACs), and different parts of classical-quantum interfaces are being utilized in new methods. The present focus of analysis in designing these interfaces is on performance and efficiency, but safety considerations additionally have to be addressed. Given the numerous recognized methods for compromising classical computer systems, it appears possible that assaults on quantum computer systems will originate in weaknesses in classical computer systems after which propagate to the quantum-classical interface.
Analysis sponsored by Microsoft Quantum Sydney outlines scalability points associated to present approaches for classical-quantum interfaces. The examine highlighted challenges associated to I/O administration, warmth and energy dissipation, system footprint, noise and interference, and bandwidth. Whereas these points are introduced in relation to scalability, the identical points present avenues for assault. As an example, attackers can leverage the warmth sensitivity to allow a denial-of-service assault or the proclivity for noise and interference to assault the integrity of operations. Our work in cybersecurity of classical computer systems has taught us that any system failure can present a gap to use a system.
Whereas securing the classical-quantum interface is a essential ingredient in quantum cybersecurity, there are different areas to handle. As an example, the output of quantum computing calculations can be way more useful to guard (and useful to steal) than most classical laptop output, given the sources essential to carry out the calculations and derive the output. As an example, a industrial pharmaceutical firm utilizing a quantum laptop to unravel a fancy chemistry downside will think about that output fairly useful as a result of it might be laborious to breed and the end-product will containly extremely useful mental property.
Furthermore, the huge computing energy in quantum computer systems necessitates defending the quantum computational energy itself. That’s, not simply defending algorithms and their outputs but additionally detecting and defending towards hijacking of quantum computing functionality, in the identical manner a botnet assault hijacks classical computing energy. For instance, if adversaries don’t have quantum computing energy of their very own, however need to carry out a resource-intensive calculation, then they might attempt to get unauthorized entry to another person’s quantum functionality. Likewise, an adversary could need to disrupt quantum-based computations solely to adversely affect the outcomes.
Lastly, a key distinction between quantum computer systems and classical computer systems is their sensitivity to temperature and the bodily world normally, which opens new vectors for denial-of-service-attacks. As an example, the refrigeration necessities for a lot of quantum architectures opens an avenue to carry out a denial-of-service assault: disrupt the cooling for these architectures and their complete operation will be halted. These are probably the most urgent of the numerous threats to quantum computer systems that the brand new self-discipline of quantum cybersecurity should tackle.”
6 Key Areas of Future Analysis in Quantum Cybersecurity
For the reason that design and structure of quantum computer systems continues to be an open space of analysis with many options being explored, it’s untimely to deal with particular vulnerabilities in particular programs. Researchers on this discipline should first type an understanding of present and future threats to quantum computer systems to develop simpler protections. The previous part highlighted numerous threats to the confidentiality, integrity, and availability of quantum computer systems. This part higlights areas of analysis wanted to develop protections towards these threats.
For instance, one key space for future analysis is the event of capabilities for monitoring quantum computations. Quantum processing can’t be monitored in the identical ways in which system monitoring is finished for classical computer systems, which makes it laborious to each assess what algorithms quantum computer systems are operating and decide whether or not malicious processing is happening. This hole illustrates the necessity for creating a multi-layered instrumentation framework for quantum computer systems, which is among the following six key areas for future quantum safety analysis we recognized within the Workshop on Cybersecurity of Quantum Computing:
- Constructing safe large-scale management programs. The size of the classical computation concerned in supporting a large-scale quantum laptop will be intensive. This assist contains management programs and error correction, however it could additionally embrace monitoring for intrusions. Analysis is required on constructing safe classical management programs for quantum computer systems.
- Enabling distributed high-performance quantum computing. Classical high-performance computing programs are usually multi-tenant and distributed. Addressing the safety of multi-tenant and distributed quantum computer systems now can lay the inspiration for safer quantum computer systems after they obtain scale.
- Understanding assault vectors on several types of quantum computer systems. Deeper analysis on potential assault vectors for numerous quantum system fashions, equivalent to whether or not adversaries solely entry quantum units via a consumer interface, is required to extra totally perceive how one can safe quantum computer systems.
- Creating formal strategies for protected and safe quantum computing programs. In computing, formal strategies consult with rigorous mathematical methods for specifying, creating, and verifying laptop software program and {hardware}. Analysis is required on creating formal strategies for quantum computing to realize reliable quantum computing.
- Developing a multi-layered instrumentation framework. Such a framework would permit security-relevant properties of quantum computer systems to be enforced or verified.
- Growing the required instruments for service suppliers to confirm quantum algorithms. These instruments will allow the power to confirm and management which algorithms are operating on a quantum laptop, additionally helps be sure that a quantum laptop won’t carry out undesirable behaviors.
Whereas all these areas of analysis are essential for shielding quantum computer systems, the panorama of cyber threats will regularly change as quantum computing know-how evolves. All of the above areas ought to be researched and, in tandem, further areas for quantum cybersecurity analysis ought to be added as they grow to be related. Strategies for shielding classical computer systems, equivalent to menace modeling and contemplating methods to compromise the rules of the confidentiality, integrity, availability (CIA) triad, have to be utilized regularly to quantum computer systems to find rising threats to analysis as this discipline of quantum cybersecurity advances.
Securing Elevated Quantum Deployment Conclusion
As quantum computing turns into extra sensible, organizations should reply many questions on how one can leverage it for strategic use. Elevated quantum deployment will elevate many technical questions on how information is ready and transferred to quantum computer systems, how algorithms are applied in quantum computer systems, and the way quantum computing outcomes are returned and verified. With all these technical concerns, an overarching query can be, How can this all be achieved securely? Right here on the CERT Division of the SEI, we’ve got a protracted historical past of defending software program and computing programs. Furthermore, when the time involves make sensible, safe selections about using quantum computer systems, we’re able to welcome you to quantum cybersecurity!