Authored by Lakshya Mathur and Sriram P
McAfee Intelligence noticed an enormous spike in extortion e-mail frauds over the previous month. The intent of those fraudulent actions is to intimidate people into paying a specified amount of cash as a ransom.
Determine 1 exhibits the variety of blackmail emails obtained over a month lately.
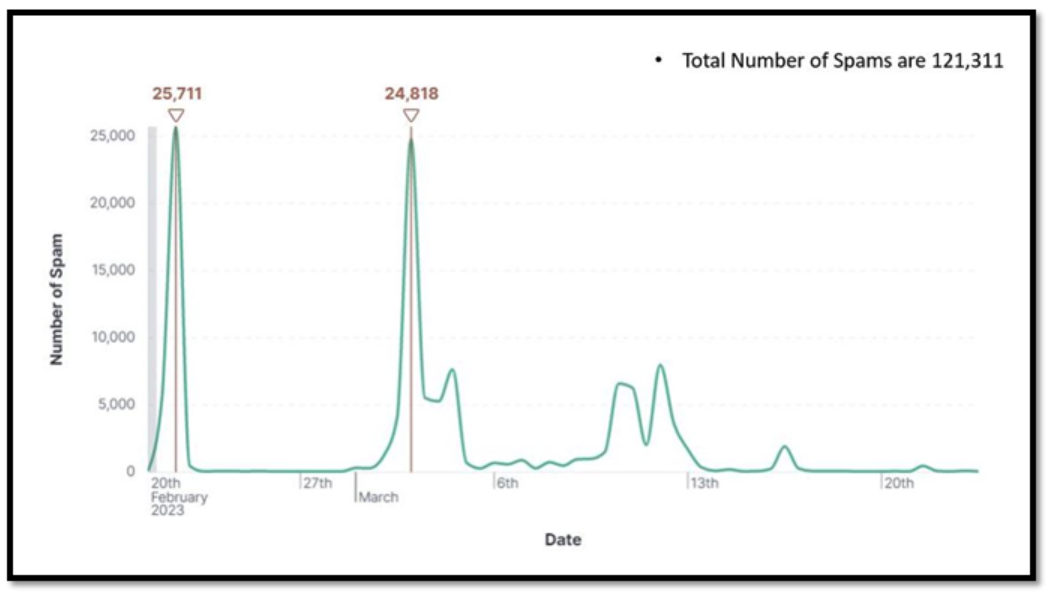
Determine 1 – Stats for 20 February 2023 – 23rd March 2023
On this weblog, we’ll delve into frauds which are changing into more and more widespread within the digital age. We’ll first outline what these frauds are and supply examples to assist readers higher perceive the character of those frauds. Moreover, we’ll discover how these frauds are on the rise, highlighting the explanations behind this development and the impression it has on people.
Lastly, we’ll present sensible recommendation to assist shoppers shield themselves from some of these assaults. This can embody a dialogue of a few of the simplest measures people can take to safeguard their private and monetary data from fraudsters.
What are Extortion Frauds?
Extortion emails are a kind of rip-off the place cybercriminals ship threatening messages to people or organizations—demanding fee in change for not releasing delicate or embarrassing data. These emails usually declare that the sender has compromising data, resembling non-public photographs or private knowledge, and threaten to share it with the recipient’s mates, household, or the general public except a fee is made. The fee is normally requested within the type of cryptocurrency, resembling Bitcoin within the current spam, which is tough to hint and could be transferred rapidly and anonymously. The aim of those emails is to scare the recipient into paying the demanded quantity, despite the fact that there won’t be any compromising data to launch.
Examples of Extortion fraud
Scammers use completely different scareware sentiments like unhealthy web shopping habits, hacking for Wi-Fi, and hacking of networks due to {hardware} vulnerabilities. We’ll now study varied illustrations of extortion emails and analyze scammers’ methods to intimidate victims into offering fee. By presenting varied real-life examples, we are able to show how scammers use scareware ways to govern and intimidate their victims into complying with their calls for. By instilling worry, the scammers hope to impress a way of urgency within the sufferer, rising the chance that they may pay the demanded ransom.
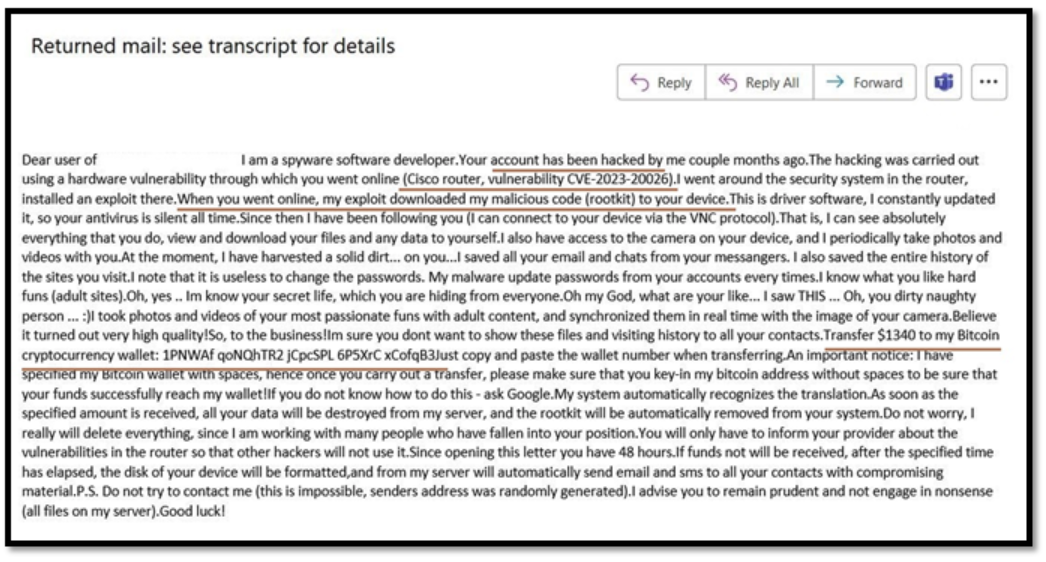
Determine 2 – Extortion fraud Instance 1
Determine 2 is an illustration of a typical extortion e-mail that scammers use to take advantage of their victims. On this occasion, the scammer is claiming to have gained unauthorized entry to the sufferer’s account by way of a safety vulnerability in a Cisco router. The scammer is then threatening to show embarrassing details about the sufferer except a fee of $1,340 is made.
The fee is demanded by way of a Bitcoin pockets handle that the scammer has offered. On this instance, the scammer has obfuscated the Bitcoin pockets handle by including areas between the characters, which is a tactic used to make it more durable to trace the fee. Now, allow us to study one other occasion of extortion emails.
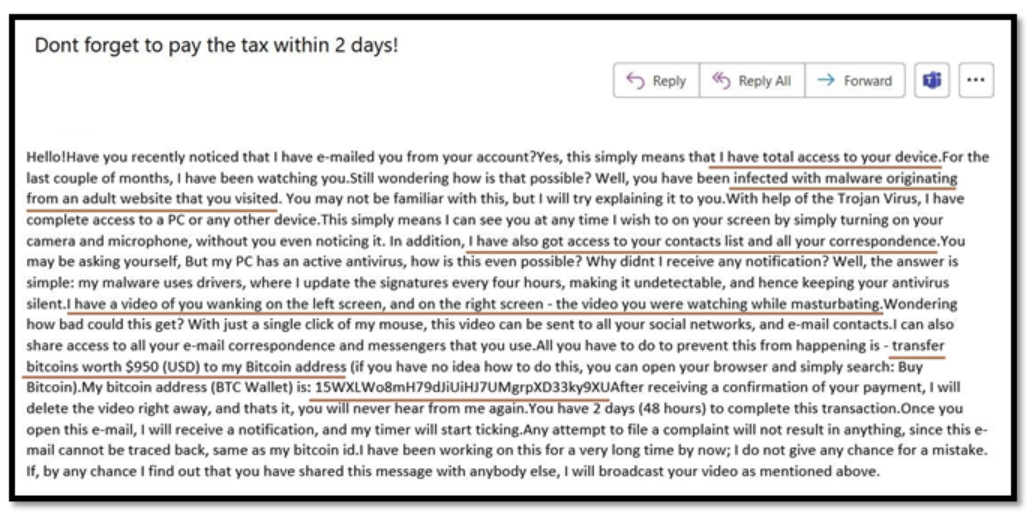
Determine 3 – Extortion fraud instance 2
Determine 3 is one other instance of an extortion e-mail that scammers use to trick and manipulate their victims. On this case, the attacker is claiming to have gained unauthorized entry to the sufferer’s accounts and has deployed trojans and viruses on the sufferer’s system. The scammer can be blackmailing the sufferer by alleging that they’ve express grownup content material concerning the sufferer and the sufferer’s net shopping historical past. The aim of that is to instill worry and provoke a way of urgency within the sufferer.
Just like the earlier instance, the scammer has offered a Bitcoin pockets handle for the sufferer to make a ransom fee of $950. Moreover, the attacker has defined that the virus they’ve deployed is undetectable by antivirus software program as a result of they’ve used drivers that replace the virus each few hours.
Use of Cryptocurrency
Cryptocurrency instruments are the most typical manner these scammers ask for a ransom. They use this tactic as a result of it’s tough to hint and could be despatched rapidly and anonymously to different platforms. We observed that scammers have been demanding ransom funds by way of Bitcoin wallets. So, we tried to assemble statistics on the variety of distinctive Bitcoin wallets we got here throughout up to now month.
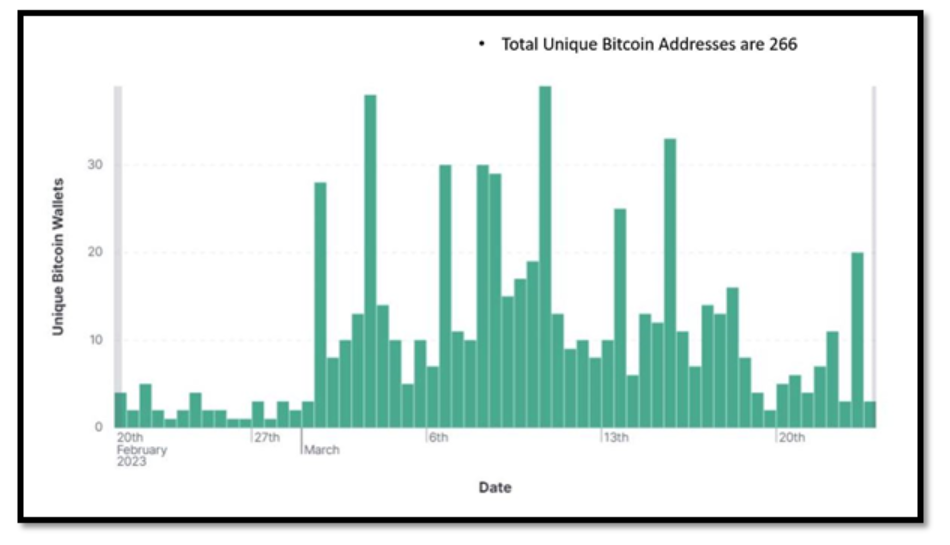
Determine 4 – Distinctive Bitcoin Stats for 20th February 2023 – 23rd March 2023
We checked these Bitcoin addresses to see what their transactions actions are and their status on the blockchain and Bitcoin abuse database. Beneath are some snapshots of the transaction of those addresses.

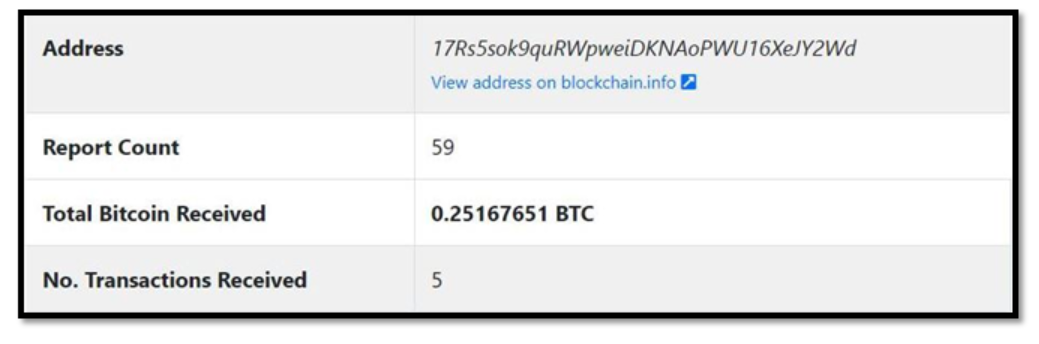
Determine 5 – Bitcoin obtained, and abuse report depend for Bitcoin handle
As illustrated in Determine 5, it’s clear that the Bitcoin addresses talked about in these extortion emails have quite a few abuse stories towards them. Moreover, some ransom funds have been obtained by way of these addresses. Our intelligence additionally collected weekly developments on how a lot cash that they had inside them.
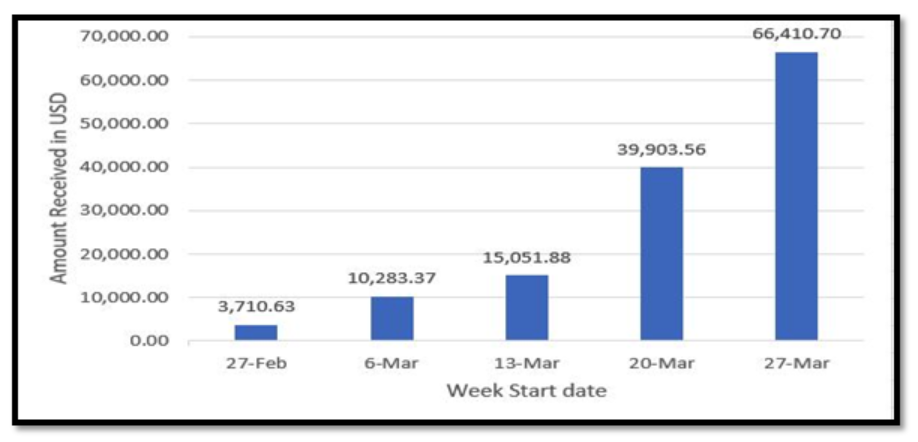
Determine 6 – Complete Quantity obtained (US Greenbacks) in that week
Determine 6 exhibits that the amount of cash obtained in these Bitcoin addresses is rising weekly. This suggests that scammers are efficiently extorting cash from extra shoppers.
Methods to keep away from these frauds?
If you happen to obtain extortion emails, comply with the steps outlined under.
- Don’t make any choices rapidly and don’t panic. If you happen to panic that will probably be a win for these scammers.
- Largely the stuff they scare you about within the mail is at all times false. As quickly as you obtain such assume twice earlier than sending fee emails, to dam them and delete them.
- Attempt to search necessary key phrases in your search engines like google, for instance, if scammers are claiming to take advantage of Cisco router vulnerabilities search that vulnerability with key phrases like ‘BTC’, ‘hack’, and another key phrases from the e-mail, and you will see that many outcomes which can enable you to to grasp that the scammer’s claims are solely false.
- Attempt to uncover extra concerning the e-mail you bought, you may seek for the sender’s handle, the topic of the mail, and even sure paragraphs from the mail on the web. You’ll certainly get data on how these emails are solely scareware.
- Preserve your self educated on such scams with the intention to shield your self.
- Preserve your antivirus up to date and do well timed full scans of your machines.
- Don’t surf on questionable net pages or obtain unlawful/cracked software program.
Regardless of developments in know-how, extortion frauds proceed to extend as seen on this weblog. Nonetheless, the most effective protection towards such scams is to stay calm, and knowledgeable, and to make others conscious of such frauds. By following the steps talked about above, resembling not responding to or paying any ransom calls for, preserving your system and software program up to date, utilizing robust passwords, and being cautious of bizarre emails or hyperlinks, you may shield your self from falling sufferer to those frauds. You will need to keep vigilant and to report any questionable exercise to the applicable authorities. By taking these precautions, you may assist stop your self and others from changing into victims of extortion fraud.

