When creating a brand new software or integrating an present one into a brand new atmosphere, consumer authentication and authorization require vital effort to be accurately carried out. Prior to now, you’ll have constructed your personal authentication system, however right now you should use an exterior identification supplier like Amazon Cognito. But, authorization logic is often carried out in code.
This would possibly start merely sufficient, with all customers assigned a job for his or her job perform. Nonetheless, over time, these permissions develop more and more complicated. The variety of roles expands, as permissions turn into extra fine-grained. New use instances drive the necessity for customized permissions. As an example, one consumer would possibly share a doc with one other in a distinct function, or a assist agent would possibly require non permanent entry to a buyer account to resolve a difficulty. Managing permissions in code is vulnerable to errors, and presents vital challenges when auditing permissions and deciding who has entry to what, notably when these permissions are expressed in numerous purposes and utilizing a number of programming languages.
At re:Invent 2022, we launched in preview Amazon Verified Permissions, a fine-grained permissions administration and authorization service on your purposes that can be utilized at any scale. Amazon Verified Permissions centralizes permissions in a coverage retailer and helps builders use these permissions to authorize consumer actions inside their purposes. Just like how an identification supplier simplifies authentication, a coverage retailer enables you to handle authorization in a constant and scalable manner.
To outline fine-grained permissions, Amazon Verified Permissions makes use of Cedar, an open-source coverage language and software program improvement package (SDK) for entry management. You may outline a schema on your authorization mannequin by way of principal varieties, useful resource varieties, and legitimate actions. On this manner, when a coverage is created, it’s validated towards your authorization mannequin. You may simplify the creation of comparable insurance policies utilizing templates. Modifications to the coverage retailer are audited to be able to see of who made the modifications and when.
You may then join your purposes to Amazon Verified Permissions via AWS SDKs to authorize entry requests. For every authorization request, the related insurance policies are retrieved and evaluated to find out whether or not the motion is permitted or not. You may reproduce these authorization requests to substantiate that permissions work as supposed.
As we speak, I’m pleased to share that Amazon Verified Permissions is usually out there with new capabilities and a simplified consumer expertise within the AWS Administration Console.
Let’s see how you should use it in follow.
Making a Coverage Retailer with Amazon Verified Permissions
Within the Amazon Verified Permissions console, I select Create coverage retailer. A coverage retailer is a logical container that shops insurance policies and schema. Authorization selections are made primarily based on all of the insurance policies current in a coverage retailer.
To configure the brand new coverage retailer, I can use completely different strategies. I can begin with a guided setup, a pattern coverage retailer (similar to for a photo-sharing app, a web based retailer, or a process supervisor), or an empty coverage retailer (advisable for superior customers). I choose Guided setup, enter a namespace for my schema (MyApp), and select Subsequent.
Sources are the objects that principals can act on. In my software, I’ve Customers (principals) that may create, learn, replace, and delete Paperwork (assets). I begin to outline the Paperwork useful resource kind.
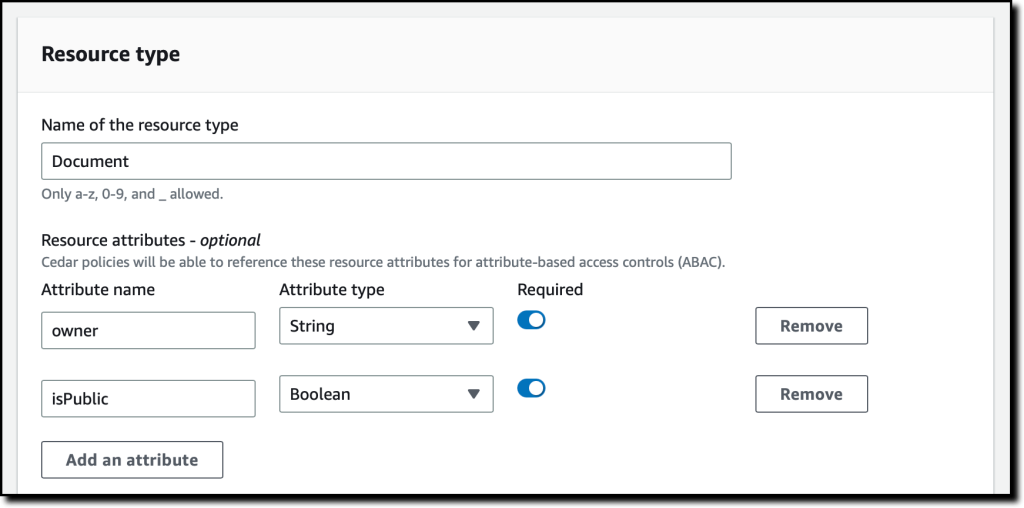
I enter the identify of the useful resource kind and add two required attributes:
proprietor(String) to specify who’s the proprietor of the doc.isPublic(Boolean) to flag public paperwork that anybody can learn.
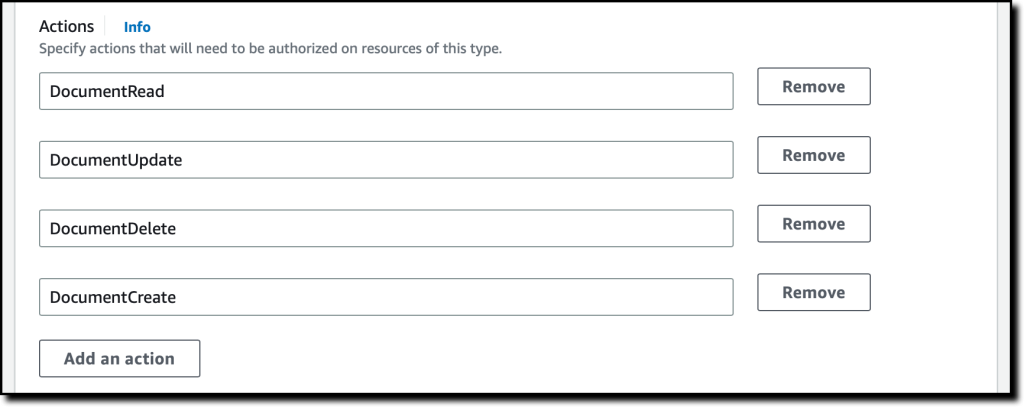
I specify 4 actions for the Doc useful resource kind:
DocumentCreateDocumentReadDocumentUpdateDocumentDelete
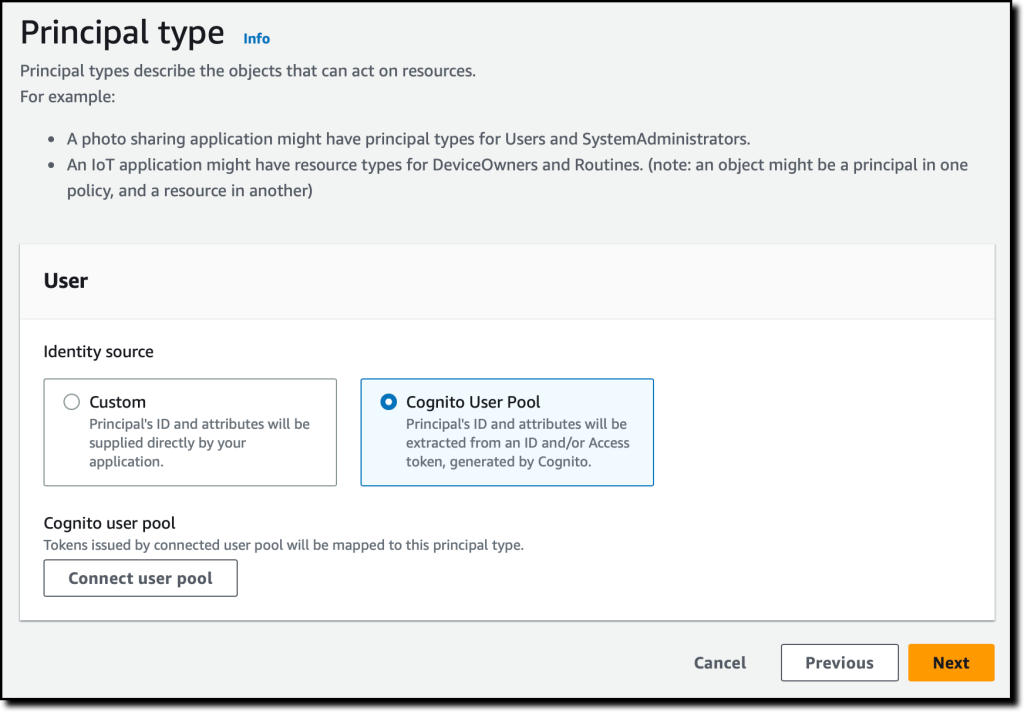
I enter Consumer because the identify of the principal kind that will likely be utilizing these actions on Paperwork. Then, I select Subsequent.
Now, I configure the Consumer principal kind. I can use a customized configuration to combine an exterior identification supply, however on this case, I exploit an Amazon Cognito consumer pool that I created earlier than. I select Join consumer pool.
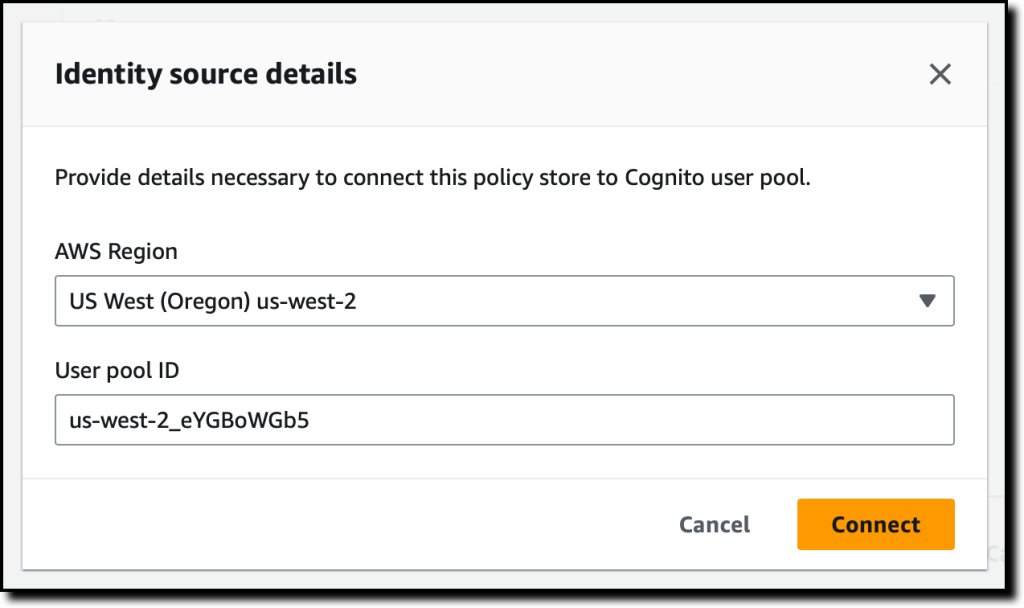
Within the dialog, I choose the AWS Area the place the consumer pool is situated, enter the consumer pool ID, and select Join.
Now that the Amazon Cognito consumer pool is linked, I can add one other degree of safety by validating the consumer software IDs. For now, I select to not use this selection.
Within the Principal attributes part, I choose which attributes I’m planning to make use of for attribute-based entry management in my insurance policies. I choose sub (the topic), used to determine the tip consumer in accordance with the OpenID Join specification. I can choose extra attributes. For instance, I can use email_verified in a coverage to present permissions solely to Amazon Cognito customers whose e-mail has been verified.
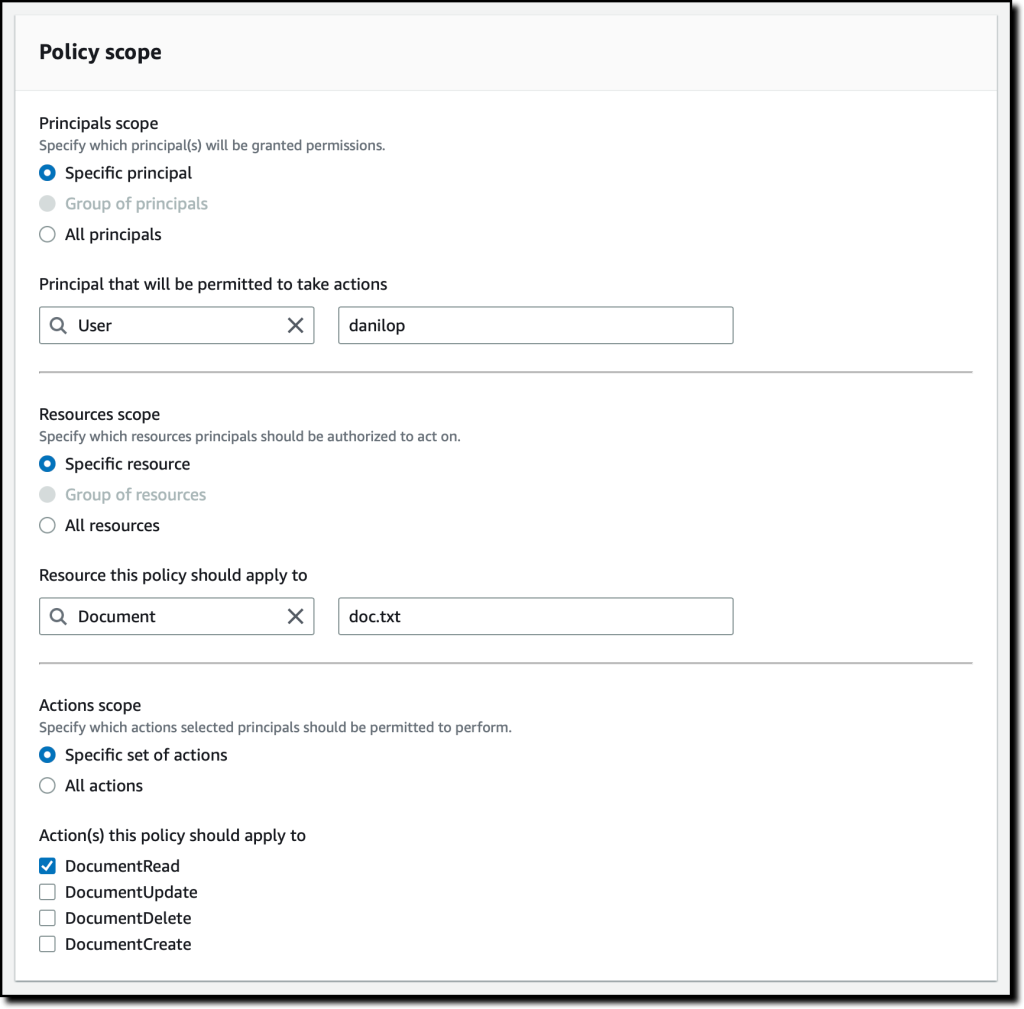
As a part of the coverage retailer creation, I create a primary coverage to present learn entry to consumer danilop to the doc.txt doc.
Within the following code, the console provides me a preview of the ensuing coverage utilizing the Cedar language.
Lastly, I select Create coverage retailer.
Including Permissions to the Coverage Retailer
Now that the coverage retailer has been created, I select Insurance policies within the navigation pane. Within the Create coverage dropdown, I select Create static coverage. A static coverage accommodates all the data wanted for its analysis. In my second coverage, I enable any consumer to learn public paperwork. By default all the things is forbidden, so in Coverage Impact I select Allow.
Within the Coverage scope, I go away All principals and All assets chosen, and choose the DocumentRead motion. Within the Coverage part, I alter the when situation clause to restrict permissions to assets the place isPublic is the same as true:
I enter an outline for the coverage and select Create coverage.
For my third coverage, I create one other static coverage to permit full entry to the proprietor of a doc. Once more, in Coverage Impact, I select Allow and, within the Coverage scope, I go away All principals and All assets chosen. This time, I additionally go away All actions chosen.
Within the Coverage part, I alter the when situation clause to restrict permissions to assets the place the proprietor is the same as the sub of the principal:
In my software, I would like to permit learn entry to particular customers that aren’t house owners of a doc. To simplify that, I create a coverage template. Coverage templates let me create insurance policies from a template that makes use of placeholders for a few of their values, such because the principal or the useful resource. The placeholders in a template are key phrases that begin with the ? character.
Within the navigation pane, I select Coverage templates after which Create coverage template. I enter an outline and use the next coverage template physique. When utilizing this template, I can specify the worth for the ?principal and ?useful resource placeholders.
I full the creation of the coverage template. Now, I exploit the template to simplify the creation of insurance policies. I select Insurance policies within the navigation pane, after which Create a template-linked coverage within the Create coverage dropdown. I choose the coverage template I simply created and select Subsequent.
To provide entry to a consumer (danilop) for a particular doc (new-doc.txt), I simply go the next values (word that MyApp is the namespace of the coverage retailer):
- For the Principal:
MyApp::Consumer::"danilop" - For the Useful resource:
MyApp::Doc::"new-doc.txt"
I full the creation of the coverage. It’s now time to check if the insurance policies work as anticipated.
Testing Insurance policies within the Console
In my purposes, I can use the AWS SDKs to run an authorization request. The console supplies a technique to to simulate what my purposes would do. I select Take a look at bench within the navigation pane. To simplify testing, I exploit the Visible mode. In its place, I’ve the choice to make use of the identical JSON syntax as within the SDKs.
As Principal, I go the janedoe consumer. As Useful resource, I exploit necessities.txt. It’s not a public doc (isPublic is false) and the proprietor attribute is the same as janedoe‘s sub. For the Motion, I choose MyApp::Motion::"DocumentUpdate".
When operating an authorization request, I can go Further entities with extra details about principals and assets related to the request. For now, I go away this half empty.
I select Run authorization request on the high to see the choice primarily based on the present insurance policies. As anticipated, the choice is enable. Right here, I additionally see which insurance policies hav been glad by the authorization request. On this case, it’s the coverage that permits full entry to the proprietor of the doc.
I can check different values. If I alter the proprietor of the doc and the motion to DocumentRead, the choice is deny. If I then set the useful resource attribute isPublic to true, the choice is enable as a result of there’s a coverage that allows all customers to learn public paperwork.
Dealing with Teams in Permissions
The executive customers in my software want to have the ability to delete any doc. To take action, I create a job for admin customers. First, I select Schema within the navigation pane after which Edit schema. Within the record of entity varieties, I select so as to add a brand new one. I exploit Position as Kind identify and add it. Then, I choose Consumer within the entity varieties and edit it so as to add Position as a guardian. I save modifications and create the next coverage:
Within the Take a look at bench, I run an authorization request to examine if consumer jeffbarr can delete (DocumentDelete) useful resource doc.txt. As a result of he’s not the proprietor of the useful resource, the request is denied.
Now, within the Further entities, I add the MyApp::Consumer entity with jeffbarr as identifier. As guardian, I add the MyApp::Position entity with admin as identifier and make sure. The console warns me that entity MyApp::Position::"admin" is referenced, but it surely isn’t included in extra entities information. I select so as to add it and repair this situation.
I run an authorization request once more, and it’s now allowed as a result of, in accordance with the extra entities, the principal (jeffbarr) is an admin.
Utilizing Amazon Verified Permissions in Your Software
In my purposes, I can run an authorization requests utilizing the isAuthorized API motion (or isAuthrizedWithToken, if the principal comes from an exterior identification supply).
For instance, the next Python code makes use of the AWS SDK for Python (Boto3) to examine if a consumer has learn entry to a doc. The authorization request makes use of the coverage retailer I simply created.
import boto3
import time
verifiedpermissions_client = boto3.consumer("verifiedpermissions")
POLICY_STORE_ID = "XAFTHeCQVKkZhsQxmAYXo8"
def is_authorized_to_read(consumer, useful resource):
authorization_result = verifiedpermissions_client.is_authorized(
policyStoreId=POLICY_STORE_ID,
principal={"entityType": "MyApp::Consumer", "entityId": consumer},
motion={"actionType": "MyApp::Motion", "actionId": "DocumentRead"},
useful resource={"entityType": "MyApp::Doc", "entityId": useful resource}
)
print('Can {} learn {} ?'.format(consumer, useful resource))
choice = authorization_result["decision"]
if choice == "ALLOW":
print("Request allowed")
return True
else:
print("Request denied")
return False
if is_authorized_to_read('janedoe', 'doc.txt'):
print("This is the doc...")
if is_authorized_to_read('danilop', 'doc.txt'):
print("This is the doc...")
I run this code and, as you may count on, the output is in keeping with the assessments run earlier than.
Availability and Pricing
Amazon Verified Permissions is on the market right now in all business AWS Areas, excluding these which can be primarily based in China.
With Amazon Verified Permissions, you solely pay for what you utilize primarily based on the variety of authorization requests and API calls made to the service. For extra data, see Amazon Verified Permissions pricing.
Utilizing Amazon Verified Permissions, you may configure fine-grained permissions utilizing the Cedar coverage language and simplify the code of your purposes. On this manner, permissions are maintained in a centralized retailer and are simpler to audit. Right here, you may learn extra about how we constructed Cedar with automated reasoning and differential testing.
Handle authorization on your purposes with Amazon Verified Permissions.
— Danilo