
VMware up to date a safety advisory printed two weeks in the past to warn clients {that a} now-patched essential vulnerability permitting distant code execution is being actively exploited in assaults.
“VMware has confirmed that exploitation of CVE-2023-20887 has occurred within the wild,” the corporate stated immediately.
This discover follows a number of warnings from cybersecurity agency GreyNoise, the primary issued one week after VMware patched the safety flaw on June 15 and simply two days after safety researcher Sina Kheirkhah shared technical particulars and proof-of-concept exploit code.
“We’ve got noticed tried mass-scanning exercise using the Proof-Of-Idea code talked about above in an try and launch a reverse shell which connects again to an attacker managed server in an effort to obtain additional instructions,” GreyNoise analysis analyst Jacob Fisher stated.
GreyNoise CEO Andrew Morris additionally alerted VMware admins of this ongoing malicious exercise earlier immediately, which seemingly prompted VMware to replace its advisory.
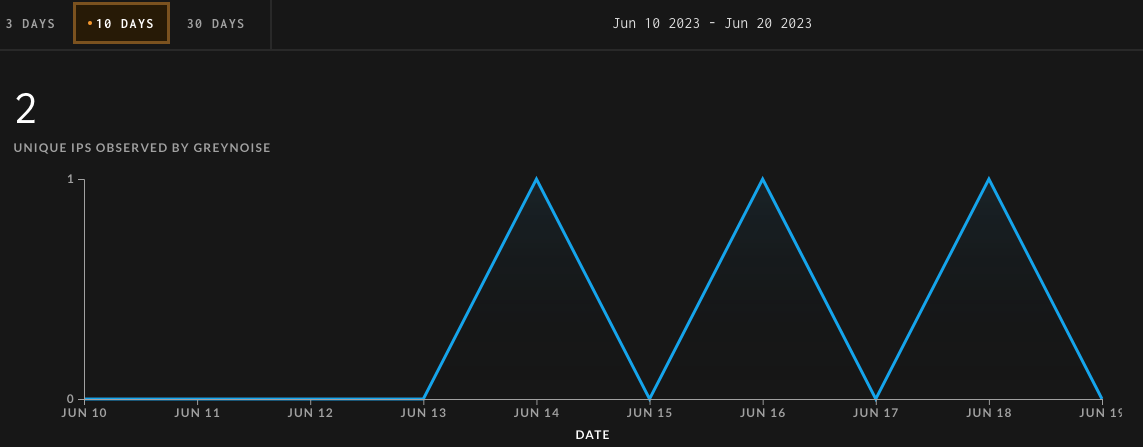
GreyNoise now gives a devoted tag to assist hold monitor of IP addresses noticed whereas making an attempt to use CVE-2023-20887.
The vulnerability impacts VMware Aria Operations for Networks (previously vRealize Community Perception), a community analytics instrument that helps admins optimize community efficiency or handle VMware and Kubernetes deployments.
Unauthenticated menace actors can exploit this command injection flaw in low-complexity assaults that do not require consumer interplay.
“VMWare Aria Operations for Networks (vRealize Community Perception) is weak to command injection when accepting consumer enter via the Apache Thrift RPC interface,” Kheirkhah defined in a root trigger evaluation of the safety bug.
“This vulnerability permits a distant unauthenticated attacker to execute arbitrary instructions on the underlying working system as the foundation consumer.”
No workarounds can be found to take away the assault vector for CVE-2023-20887, so admins should patch all VMware Aria Operations Networks 6.x on-prem installations to make sure they’re safe from ongoing assaults.
An entire record of safety patches for all weak Aria Operations for Networks variations is on the market on VMware’s Buyer Join web site.
